Difference between revisions of "HTTPS Provisioning"
Kevin Wilkie (Talk | contribs) |
Kevin Wilkie (Talk | contribs) |
||
| (5 intermediate revisions by one user not shown) | |||
| Line 11: | Line 11: | ||
All keystore management is performed using the java /opt/java/bin/keytool command. | All keystore management is performed using the java /opt/java/bin/keytool command. | ||
| − | + | Change into the folder with the keystore | |
cd /opt/ros/resources/prepos/ | cd /opt/ros/resources/prepos/ | ||
| − | |||
| + | Generate a private key | ||
| + | keytool -genkey -alias tomcat -keyalg RSA -keystore roskeystore_new.jks -storepass password -dname "...." | ||
| − | + | Generate a CSR | |
| − | + | keytool -certreq -keyalg RSA -alias tomcat -file certreq.csr -keystore roskeystore_new.jks -storepass password | |
| + | |||
| + | Import certificate into keystore | ||
| + | keytool -import -alias tomcat -keyalg RSA -keystore roskeystore_new.jks -trustcacerts -file certnew.cer -storepass password | ||
| + | |||
| + | If you've change the keystore location or password, update anuview Flow to reflect this and restart the service. | ||
| + | |||
| + | '''Optional''' | ||
| + | Generating a new keystore and self signed cert in /opt/ros/resources/prepos/roskeystore_new.jks | ||
| + | cd /opt/ros/resources/prepos/ | ||
| + | keytool -genkey -keyalg RSA -alias selfsigned -keystore roskeystore_new.jks -storepass password -validity 360 -keysize 2048 | ||
Removing an unrequired certificate | Removing an unrequired certificate | ||
keytool -delete -alias cashelros -keystore roskeystore_kw.jks | keytool -delete -alias cashelros -keystore roskeystore_kw.jks | ||
| + | |||
| + | |||
| + | if a certificate is to work in Chorme it must have a SAN entry. This has been a requirement in Chrome for the last 2 years. It does not appear that other browsers have this requirement | ||
| + | Generate Private key | ||
| + | keytool -genkey -alias tomcat -keyalg RSA -keystore roskeystore_new.jks -storepass password -dname "CN=gigaflow.company.net " | ||
| + | |||
| + | Gererate CSR | ||
| + | keytool -certreq -keyalg RSA -alias tomcat -file certreq.csr -keystore roskeystore_new.jks -storepass password -ext SAN=dns:gigaflow,dns:gigaflow.company.net | ||
| + | |||
| + | you can check your csr file to ensre that the san entires are present by | ||
| + | keytool -printcertreq -file certreq.csr -v | ||
| + | |||
| + | |||
| + | For client requests from the server you must add the certs to the JRE ca store. Password is changeit | ||
| + | keytool -import -trustcacerts -file [certificate] -alias [alias] -keystore JAVA_HOME/lib/security/cacerts | ||
| + | |||
| + | |||
| + | If you already have a crt and private key file you can create a new keystore by first creating a pkcs12 file | ||
| + | openssl pkcs12 -export -in [<em>filename-certificate</em>] -inkey [<em>filename-key</em>] -name [<em>host</em>] -out [<em>filename-new</em>-PKCS-12.p12] | ||
| + | keytool -importkeystore -deststorepass [password] -destkeystore [filename-new-keystore.jks] -srckeystore [filename-new-PKCS-12.p12] -srcstoretype PKCS12 | ||
Revision as of 09:21, 20 October 2020
You can view and change which ketstore is in use for SSL in the SSL panel of the Settings page
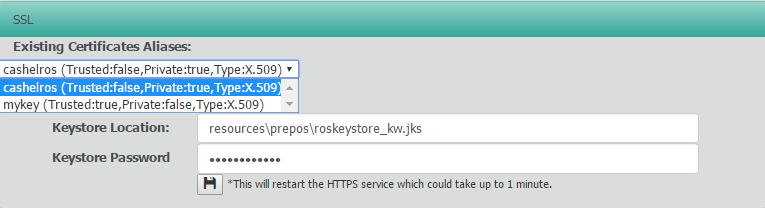
Here you can use the drop down to view the certificates in the current keystore.
We highly recommend you use a different keystore name as future updates may overwrite the existing file.
In this example, we've copied the origional keystore (/opt/ros/resources/prepos/roskeystore.jks to /opt/ros/resources/prepos/roskeystore_new.jks) We've kept the same default keystore password "cashelros254"
All keystore management is performed using the java /opt/java/bin/keytool command.
Change into the folder with the keystore
cd /opt/ros/resources/prepos/
Generate a private key
keytool -genkey -alias tomcat -keyalg RSA -keystore roskeystore_new.jks -storepass password -dname "...."
Generate a CSR
keytool -certreq -keyalg RSA -alias tomcat -file certreq.csr -keystore roskeystore_new.jks -storepass password
Import certificate into keystore
keytool -import -alias tomcat -keyalg RSA -keystore roskeystore_new.jks -trustcacerts -file certnew.cer -storepass password
If you've change the keystore location or password, update anuview Flow to reflect this and restart the service.
Optional Generating a new keystore and self signed cert in /opt/ros/resources/prepos/roskeystore_new.jks
cd /opt/ros/resources/prepos/ keytool -genkey -keyalg RSA -alias selfsigned -keystore roskeystore_new.jks -storepass password -validity 360 -keysize 2048
Removing an unrequired certificate
keytool -delete -alias cashelros -keystore roskeystore_kw.jks
if a certificate is to work in Chorme it must have a SAN entry. This has been a requirement in Chrome for the last 2 years. It does not appear that other browsers have this requirement
Generate Private key
keytool -genkey -alias tomcat -keyalg RSA -keystore roskeystore_new.jks -storepass password -dname "CN=gigaflow.company.net "
Gererate CSR
keytool -certreq -keyalg RSA -alias tomcat -file certreq.csr -keystore roskeystore_new.jks -storepass password -ext SAN=dns:gigaflow,dns:gigaflow.company.net
you can check your csr file to ensre that the san entires are present by
keytool -printcertreq -file certreq.csr -v
For client requests from the server you must add the certs to the JRE ca store. Password is changeit
keytool -import -trustcacerts -file [certificate] -alias [alias] -keystore JAVA_HOME/lib/security/cacerts
If you already have a crt and private key file you can create a new keystore by first creating a pkcs12 file
openssl pkcs12 -export -in [filename-certificate] -inkey [filename-key] -name [host] -out [filename-new-PKCS-12.p12] keytool -importkeystore -deststorepass [password] -destkeystore [filename-new-keystore.jks] -srckeystore [filename-new-PKCS-12.p12] -srcstoretype PKCS12