Documentation >
Reference Manual for GigaFlowFigure: GigaFlow's login screen

- Go to gigaflow.viavi.com from any browser.
- Log in using your credentials.
- GigaFlow will open on the Dashboards welcome screen.
The left menu contains links to the main outputs from GigaFlow.
Figure: Detail of the left main menu

The top menu contains links to system configuration, system settings and user settings.
Figure: Detail of the top main menu

Most items in GigaFlow will have a white information button on a gray background at the top right. Click this to link out to the relevant section in the GigaFlow Reference Manual.
You can refresh any page in GigaFlow using the browser refresh button.
By clicking, holding and dragging left or right, you can create a report for any shorter time period.
Figure: Click and drag to create a report for a particular timeframe within a timeline

The user selects a shorter time period of interest by clicking and dragging, in this case from just before 11:00 to just before 11:15.
Figure: Re-scaled timeline

The timeline is re-drawn for the selected time period. All associated information on this page is recalculated, i.e. tables and graphs.
Throughout GigaFlow, all hyperlinks are colored blue.
The system search is at the top of every GigaFlow page; it is a powerful and convenient way to access information directly, returning relevant matches and detailed summary information.
The left hand side of the search results screen displays summary information about that IP address, including:
- Infrastructure device(s) that this IP address was seen on.
- More information about the associated device.
- Associated interfaces.
- Detail about the IP address.
- Associated traffic groups.
- Associated ARP entries.
- Associated LLDP entries.
- Associated events, e.g. watchlist or profile alerts.
The Treeview, a kind of graphical flow mapping, will automatically load on the right hand side of the search results screen. This is a visual representation of the in- and out- traffic associated with a selected device.
See Search > Graphical Flow Mapping for more.
- Enter an IP address in the Search box.
- Click Go.
- Select a reporting period and click Submit
 .
.
Figure: GigaFlow's search bar and results screen. In this screenshot, the user is searching for an IP address, 172.21.21.254.

Scrolling down reveals additional results:

Click to expand.The tabbed box on the left displays search results for that IP address, including any infrastructure device that it is associated with, the number of interfaces it was recently seen on, IP entry details, ARP entries and the number of secflow events associated with it.
Each item can be clicked to display more information and follow-on searches can be carried out for linked information, e.g. for associated MAC addresses.
GigaFlow can search by MAC address. This returns the name of the connected device and its VLAN.
To search by MAC address:
- Enter the entire MAC address into the search box.
- GigaFlow's MAC address search works for any standard MAC address format.
After searching the MAC address a number of key pieces of information will be displayed, including:
- IP address.
- Host name.
- MAC vendor.
- Layer-3 devices, interfaces or interface tools.
From here, some of the other actions you can take include:
- Click the interface displayed in the left had dialog box to access more information about the physical interface the device is connected to. The interface with the lowest MAC count is the connected interface.
- Click Live View on the right to display the live in- and out- utilisation of the interface.
- Live View also provides speed, duplex and error count information for the interface.
- Click on Connections to see what other devices are connected to the same port.
To search by username:
- Enter a username, or part of a username, into the search box.
- GigaFlow will tell you if that username, or any variation of it, has been seen on your network.
- Click on any of the search results to display its associated information in the right-hand side panel.
To search for a specific network switch:
- Enter the switch IP address into the search box.
- Click to expand the Device information and click, See all connections.
- The Device Connections table shows connections to any one port on any one VLAN.
- You can filter information by entering an interface, or device etc., into the search bar at the top-right of the table.
To make a follow-on search from a specific device or switch:
- Using switches from previously displayed tables, you can search for any switches of similar origin, e.g containing the prefix of PATS-3560.
- Click on the desired switch; this reopens the Device Connections table.
- You can also search by VLAN.
GigaFlow Search provides access to the Graphical Flow Mapping feature. Searching for any IP address returns summary tables as well as a visualisation of flows during the reporting period selected.
To access this feature, search for an IP address. See Searching by IP Address above.
On the right hand side of the screen, you will see the Graphical Flow Map.
Figure: GigaFlow's Graphical Flow Map

The Graphical Flow Map is an interactive visualisation of the flows associated with that IP address. The branches of the Graphical Flow Map can be expanded to show associated interfaces and destination and source devices. These in turn can be explored.
To explore the Graphical Flow Map:
- Click on any icon to show more information.
- Click on the Destination Apps icon or the Source Apps icon for a breakdown of the applications. You can click on these to expand the tree.
- Click + to see more devices in a tree of many branches.
- The size of the line linking any two devices is proportional to the traffic volume between them.
- Click on any line in the Treeview table to filter only inbound or only outbound traffic. This will open a report showing traffic for the past two hours.
See also Profiling > Events > Flow Details
After logging in, you will see the Server Overview Dashboard. From here you have direct access to some of GigaFlow's main functions.
Figure: GigaFlow's main dashboard

Located at Dashboards > Performance Overview.
This is a summary of traffic across the busiest infrastructure devices over the past hour. Infrastructure devices are routers sending flow as well as other Layer-2 devices that are not sending flow but sending ARP and CAM Tables. The information displayed includes:
- Avg Bits/s: average traffic per second per device.
- Percentage: this is the proportion of all traffic over the past hour seen by a particular system/router.
- Position relative to the same hour last week: this is the percentage increase or decrease in traffic per second per device compared with the same hour last week.
When more than ten devices are registered, the full list can be displayed by clicking the drill down icon. This displays a tabular version of all the data, with a CSV export option.
This is a summary of traffic across the busiest interfaces over the past hour. The information displayed includes:
- Avg Bits/s: average traffic per second.
- Max: this is maximum traffic volume seen in the data set.
- Percentage: this is the proportion of all traffic seen by a particular interface.
- Position relative to the same hour last week: this is the percentage increase or decrease in traffic per second per interface compared with the same hour last week.
When more than ten interfaces are registered, the full list can be displayed by clicking the drill down icon. This displays a tabular version of all the data, with a CSV export option.
See Configuration > Infrastructure Devices for setup instructions.
This graph shows the traffic associated with the busiest traffic groups over the past hour. The information displayed includes:
- Avg Bits/s: average traffic per second per traffic group.
- Percentage: this is the proportion of all traffic over the past hour seen by a particular traffic group.
- Position relative to the same hour last week: this is the percentage increase or decrease in traffic per second per traffic group compared with the same hour last week.
When more than ten traffic groups are registered, the full list can be displayed by clicking the drill down icon. This displays a tabular version of all the data, with a CSV export option.
This graph shows the traffic associated with the busiest applications over the past hour. The information displayed includes:
- Avg Bits/s: average traffic per second per application.
- Percentage: this is the proportion of all traffic over the past hour seen by a particular application.
- Position relative to the same hour last week: this is the percentage increase or decrease in traffic per second per application compared with the same hour last week.
When more than ten applications are registered, the full list can be displayed by clicking the drill down icon. This displays a tabular version of all the data, with a CSV export option.
This graph shows the traffic associated with the busiest source IPs in the past hour. The information displayed includes:
- Avg Bits/s: average traffic per second per source IP.
- Percentage: this is the proportion of all traffic over the past hour seen by a particular source IP.
- Position relative to the same hour last week: this is the percentage increase or decrease in traffic per second per source IP compared with the same hour last week.
When more than 10 IP addresses are registered, the full list can be displayed by clicking the drill down icon. This displays a tabular version of all the data, with a CSV export option.
This graph shows the traffic associated with the busiest destination IPs in the past hour. The information displayed includes:
- Avg Bits/s: average traffic per second per source IP.
- Percentage: this is the proportion of all traffic over the past hour seen by a particular destination IP.
- Position relative to the same hour last week: this is the percentage increase or decrease in traffic per second per destination IP compared with the same hour last week.
When more than 10 IP addresses are registered, the full list can be displayed by clicking the drill down icon. This displays a tabular version of all the data, with a CSV export option.
Located at Dashboards > Server Overview.
Figure: Detail of the left main menu and Dashboards submenu.

This default welcome screen shows summary server flow information with three main sections:
This is a summary of traffic across all of your infrastructure devices ranked by the busiest network device. Infrastructure devices are routers sending flow as well as other Layer-2 devices that are not sending flow but sending ARP and CAM Tables. The information displayed includes:
- Avg Bits/s: average traffic per second.
- Max: this is maximum traffic volume seen in the data set.
- Percentage: this is the proportion of all traffic seen by particular system/router.
The bars on the graph indicate the volume of data seen over the reporting period, by default 2 hours.
This is a graph and table of interface bit rates, with a breakdown by individual interface. This is a summary of the busiest interfaces across your network.
See Configuration > Infrastructure Devices for setup instructions.
When more than 10 devices are registered, the full list can be displayed by clicking List All Drill down icon. beside the table title.
The CSV link at the top right of the table generates a .csv export.
This middle graph shows all events and alerts across your network during the reporting period.
Figure: Detail of GigaFlow's report period selection panel, at the top of most pages
- The reporting period is shown at the top right of the main body of the page. This is 2 hours by default.
- On login, the system displays information for the default time period.
- This default time period can be set in Configuration > Reporting in the main menu.
- Different reporting periods can be selected by clicking the from and to boxes.
Figure: Clicking in either the From or To field brings up a date and time selector.

Click once on any infrastructure device IP address or interface in the tables and you will be taken to an overview report for that device or interface. You can access the same overview using GigaFlow's search function. Search for the IP address and in the main left-hand side table, click the Infrastructure Device name. In the right-hand side table, click Overview.
See Dashboards > Device Overview and Dashboards > Interface Overview.
Located at Dashboards > Device Overview; there is also a unique Device Overview subpage for each infrastructure device.
From the Dashboards menu, the Device Overview option displays:
- Busiest devices in the past hour.
- Summary devices.
This information is also displayed in Performance Overview and in Server Overview. See Dashboards > Performance Overview > Top Devices (Last Hour v Last Week Hour) and Dashboards > Server Overview.
Device Overview Subpages
Click once on any infrastructure device IP address or interface in the tables and you will be taken to an overview report for that device or interface. You can access the same overview using GigaFlow's search function. Search for the IP address and in the main left-hand side table, click the Infrastructure Device name. In the right-hand side table, click Overview.
The overview for each infrastructure device includes graphs and tables with useful information. These include:
This panel lists the most important device information, including:
- IP address.
- Display name.
- SysName.
- SysLocation.
- SNMP status.
- ARP entries.
- CAM entries.
- System description.
You can add an Attribute, or alias, for network infrastructure by selecting from the interface Attributes drop down selector. See Configuration > Attributes for more on attributes. This panel lists attributes and useful tools associated with the selected device, including:
Attributes. See Configuration > Infrastructure Devices and click on any device for more.Links out to useful tools, including Forensics, ARPs, CAMs, Live Interfaces and Traffic Overview.Links to associated integrations. See System > Global for more about integrations.
Figure: Visual from Device Overview subpage

The information is presented as a pie-chart. Each application can be queried by clicking the drill down icon for more.
This graph shows the top 10 ports/applications associated with this device in the past hour.
This graph shows the top 10 traffic group pairs associated with this device in the past hour.
This graph shows the top 10 source IPs associated with this device in the past hour.
This graph shows the top 10 destination IPs associated with this device in the past hour.
This graph shows the summary traffic volume information for this device (MB/s).
This graph shows the summary interface traffic volume information for this device (MB/s).
A timeline of threat events associated with the device in the report period.
A table of all the interfaces associated with this device is displayed at the bottom of the page; the information presented includes:
- The device name.
- The ifIndex of the interface.
- The name of the interface.
- A description of the interface.
- Any alias given by the local user.
- The IP address associated with the interface.
- The nominal inward flow rate (MB/s), defined by the user.
- The nominal outward flow rate (MB/s), defined by the user.
- The average inward flow rate as a percentage of the nominal inward flow rate.
- The average inward flow rate (MB/s).
- The maximum inward flow rate as a percentage of the nominal inward flow rate.
- The maximum inward flow rate (MB/s).
- The average outward flow rate as a percentage of the nominal outward flow rate.
- The average inward flow rate (MB/s).
- The maximum outward flow rate as a percentage of the nominal outward flow rate.
- The maximum outward flow rate (MB/s).
Located at Dashboards > Interface Overview; there is also a unique Interface Overview subpage for each interface.
From the Dashboards menu, the Interface Overview option displays high-level summary information; some of this is also displayed in Server Overview. See Dashboards > Server Overview. The three graphs displayed are:
- Top Interfaces In (Last Hour v Last Week Hour), i.e. the interfaces with heaviest inward traffic over the past hour. This is compared to the same hour last week.
- Top Interfaces Out (Last Hour v Last Week Hour), i.e. the interfaces with heaviest outward traffic over the past hour. This is compared to the same hour last week.
- Summary Interfaces.
- Summary Interfaces Peak.
Figure: GigaFlow's Interface Overview page

Click once on any infrastructure device IP address or interface in the tables and you will be taken to an overview report for that device or interface. You can access the same overview using GigaFlow's search function. Search for the IP address and in the main left-hand side table, click the Infrastructure Device name. In the right-hand side table, click Overview.
Dedicated Interface Overview Pages
At the top of the page, you can see:
This panel displays the interface details:
- IfIndex: the interface number.
- The interface name.
- The interface alias.
- The interface description.
- The interface IP address.
- The interface MAC address.
- Speed In (MB/s).
- Speed Out (MB/s).
- Admin status.
- Oper status.
You can edit these at Configuration > Infrastructure Devices.
You can add an Attribute, or alias, for an interface by selecting from the interface Attributes drop down selector. See Configuration > Attributes for more. This panel lists attributes and useful tools associated with the selected interface, including:
- Attributes.
- Links out to useful tools, including Forensics, ARPs, CAMs, Live Interfaces and Traffic Overview.
- Links to associated integrations. See System > Global for more about integrations.
In addition, you will see graphs and tables of:
This is a summary of the total traffic for that interface.
This is a summary of the total inward traffic for that interface.
This is a summary of the total outward traffic for that interface.
This is a summary of the total inward packets for that interface.
This is a summary of the total outward packets for that interface.
A summary of the total inward flows for that interface.
This is a summary of the total outward flows for that interface.
DSCP (differentiated services code point) in summary information used for ingress policing configuration.
DSCP (differentiated services code point) out summary information used for ingress policing configuration.
DSCP (differentiated services code point) in summary information used for egress policing configuration.
DSCP (differentiated services code point) out summary information used for egress policing configuration.
Application traffic overview.
This graph shows the traffic associated with the busiest applications over the past hour. The information displayed includes:
- Avg Bits/s: average traffic per second per application.
- Percentage: this is the proportion of all traffic over the past hour seen by a particular application.
- Position relative to the same hour last week: this is the percentage increase or decrease in traffic per second per application compared with the same hour last week.
When more than ten applications are registered, the full list can be displayed by clicking the drill down icon. This displays a tabular version of all the data, with a CSV export option.
This graph shows the top 10 source IPs over the past hour; this is compared with the same hour a week before.
This graph shows the top 10 destination IPs over the past hour; this is compared with the same hour a week before.
This is a graph and table of traffic group bit rates, with a breakdown by individual traffic group. This is a summary of the busiest traffic groups across your network.
See Configuration > Traffic Groups for setup instructions.
When more than 10 traffic groups are registered, the full list can be displayed by clicking List All Drill down icon. beside the table title.
The CSV link at the top right of the table generates a .csv export.
This section provides an overview of the traffic associated with source IPs.
This graph shows the traffic associated with the busiest applications over the past hour. The information displayed includes:
- Avg Bits/s: average traffic per second per application.
- Percentage: this is the proportion of all traffic over the past hour seen by a particular application.
- Position relative to the same hour last week: this is the percentage increase or decrease in traffic per second per application compared with the same hour last week.
When more than ten applications are registered, the full list can be displayed by clicking the drill down icon. This displays a tabular version of all the data, with a CSV export option.
This graph shows the top 10 destination IPs over the past hour.
This graph shows the top 10 destination IPs over the past hour.
This is a graph and table of traffic source IP bit rates, with a breakdown by individual traffic group. This is a summary of the busiest traffic source IPs across your network.
When more than 10 traffic source IPs are registered, the full list can be displayed by clicking List All Drill down icon. beside the table title.
The CSV link at the top right of the table generates a .csv export.
This section provides an overview of the traffic associated with destination IPs.
This graph shows the traffic associated with the busiest applications over the past hour. The information displayed includes:
- Avg Bits/s: average traffic per second per application.
- Percentage: this is the proportion of all traffic over the past hour seen by a particular application.
- Position relative to the same hour last week: this is the percentage increase or decrease in traffic per second per application compared with the same hour last week.
When more than ten applications are registered, the full list can be displayed by clicking the drill down icon. This displays a tabular version of all the data, with a CSV export option.
This graph shows the top 10 source IPs over the past hour.
This graph shows the top 10 destination IPs over the past hour.
This is a graph and table of traffic destination IP bit rates, with a breakdown by individual traffic group. This is a summary of the busiest traffic destination IPs across your network.
When more than 10 traffic destination IPs are registered, the full list can be displayed by clicking List All Drill down icon. beside the table title.
The CSV link at the top right of the table generates a .csv export.
Located at Dashboards > Traffic Group Overview; there is also a unique Traffic Group Overview subpage for each Traffic Group.
From the Dashboards menu, the Traffic Group option displays summary information.
Traffic Group Subpages
Click once on any Traffic Group name in the table and you will be taken to an overview report for that Traffic Group. .
Click once on any of the "Down Arrows" beside the Traffic Group name in the table and you will be taken to the forensics report for that Traffic Group.
The overview for each Traffic Group includes graphs and tables with useful information (similar to device overviews). These include:
This graph shows the top 10 destination IPs over the past hour.
This graph shows the top 10 destination IPs over the past hour.
This graph shows the top 10 source IPs over the past hour.
This graph shows the top 10 destination IPs over the past hour.
This graph shows the source traffic associated with traffic groups over the past hour. The information displayed includes:
- Avg Bits/s: average traffic per second per application.
- Percentage: this is the proportion of all traffic over the past hour seen by a particular traffic group.
- Position relative to the same hour last week: this is the percentage increase or decrease in traffic per second per traffic group compared with the same hour last week.
When more than ten traffic group are registered, the full list can be displayed by clicking the drill down icon. This displays a tabular version of all the data, with a CSV export option.
This graph shows the destination traffic associated with traffic groups over the past hour. The information displayed includes:
- Avg Bits/s: average traffic per second per application.
- Percentage: this is the proportion of all traffic over the past hour seen by a particular traffic group.
- Position relative to the same hour last week: this is the percentage increase or decrease in traffic per second per traffic group compared with the same hour last week.
When more than ten traffic group are registered, the full list can be displayed by clicking the drill down icon. This displays a tabular version of all the data, with a CSV export option.
Located at Dashboards > Events.
From the Dashboards menu, the Events option displays summary information about events and exceptions. See also Dashboards > Server Overview. You can also click on Events item in the main menu to access the same information.
Some things that will trigger an event record include:
- Attempts to access blacklisted resources.
- Profile exceptions, i.e. behaviours deviating from norms. These are user defined at Configuration > Profiling.
- SYN flood event(s).
- Lost neighbour(s).
- New device(s) sending flows.
- Connected device(s) suddenly not sending flows.
On the Events page, you can see:
A timeline of all events in the reporting period, the Events Graph. A tabulated version of this information is shown underneath.
Figure: Events Graph

- Infographic of the number of event types by date and time; this is the Event Types infographic. Circle size indicates the number of events.
- Infographic of the frequency of occurence of particular event categories by date and time, i.e. number of times per time interval; this is the Event Categories infographic. Circle size indicates frequency.
- Infographic of the frequency of an event triggered by a particular source host by date and time; this is the Event Source Host(s) infographic. Circle size indicates frequency.
- Infographic of the frequency of an event targetted at a particular host by date and time, i.e. number of times per time interval; this is the Event Target Host(s) infographic. Circle size indicates frequency.
Figure: Event Categories infographic

- Infographic of the frequency with which each infrastructure device was affected by an event by date and time, i.e. number of times per time interval; this is the Infrastructure Devices infographic. Circle size indicates frequency.
- Infographic of the frequency of an event by the measure of confidence in its identification, i.e. your confidence in the completeness and accuracy of the blacklist that the IP address was found in, and the severity of the threat to your network infrastructure, i.e. number of times per time interval; this is the Confidence & Severity infographic. Circle size indicates frequency.
Figure: Confidence & Severity infographic

By clicking once on any legend item, you will be taken to a detailed report, e.g. detailed reports for each Event Type, Source Host, Infrastructure Device, Event Category and Target Host.
To view a world map overlaid with attack/event trajectories, click on the Threat Map main menu item.
- Select the report period using the Window pull-down menu, e.g. select 12 hours to view threat data for the past 12 hours.
- A timeline above the main map displays threats during the report period.
- Threat trajectories are displayed on the main map in the centre of the screen.
Figure: The main threat map visualization

Alongside the map, you will see the expandable tables:
- Threat Src Locations: a list of the countries where the threats originate.
- Event IP Sources: a list of the IPs associated with the threats.
- Event Types: a list of the types of threat identified .
- Event Categories: a list of the threat categories.
- Event Devices: a list of your infrastructure devices involved in the threat.
- Threat Dest Locations: a list of the countries where devices affected by the threats reside.
- Event IP Dests: a list of the IP addresses affected by the threats, i.e. where did the data go.
Most items in the side tables can be examined in isolation, i.e. Event IP Sources, Event Types, Event Categories, Event Devices, Event IP Destinations.
- To focus on a single event IP source:
Click on the relevant IP and the page will display information related only to that IP.The main table below the map displays a complete summary of the the threats mapped with time. In addition to the information presented in the side tables, the main table includes:
- The protocol/application involved.
- The byte-size of the threat event.
- The number of packets involved in the threat event.
See Dashboards > Events.
The Profiling main menu item has three options: Realtime Overview, Event Dashboard and Traffic Groups.
Profiles help you to understand the normal behaviour of your network. For more, and to create profiles, go to Configuration > Profiling.
Profiling > Realtime Overview
The Realtime Profiling Status shows realtime data on defined Profilers. The display updates every 5 seconds and shows:
- Profiler: this is the defined profile.
- Clients: the number of connected devices.
- Hits: the number of flow records that have matched the allowed flows.
- Exceptions: the flow records for this profile that have deviated from the ideal, or Allowed, profile. See Configuration > Profiling.
Located at Profiling > Profiling Events.
The Profiling Event Dashboard gives an overview of profile events.
Figure: The Profiling Events page

At the top of the page you can set both the reporting period and resolution, from one minute to 4 weeks.
This infographic shows a timeline of the number of events with the profile(s) involved. Circle diameters represent the number of events. The peak number of events in the timeline for each profile are highlighted in red.
This infographic shows a timeline of the number of events along with their estimated severity level(s). Circle diameters represent the number of events. The peak number of events in the timeline for each severity level are highlighted in red.
Event Entries is dynamically generated; you must click Click To Load to populate the table. The Event Entries table gives a breakdown of profile events with the following entries:
- The unique event ID number.
- The time at which event occurred.
- The category or profile name.
- The severity of the event as a percentage.
- The source IP address.
- The target IP address.
- The application, user defined if it exists. See also Configuration > Profiling and Flow Details.
- Any information other error/status message, e.g. Profiler Exception.
A drop-down selector lets you choose the number of the most events to display.
To access a detailed overview of any flow, click on the adjacent Drill Down icon  . This provides a complete overview of that flow, listing:
. This provides a complete overview of that flow, listing:
- The source address, a link to search forensics and any associated blacklists.
- Source MAC address.
- Destination address, a link to search forensics and any associated blacklists.
- Destination MAC address.
- Source port.
- Destination port.
- Appid: the application ID is a unique identifier for each application.
- In GigaFlow, Appid is a positive or negative integer value. The way in which the Appid is generated depends on which of the 3 ways the application is defined within the system. Following the hierarchy outlined in Configuration > Profiling -- Apps/Options -- Defined Applications, a negative unique integer value is assigned if (1) the application is associated with a Profile Object or (2) if it is named in the system. If the application is given by its port number only (3), a unique positive integer value is generated that is a function of the lowest port number and the IP protocol.
- Application. See Appid, above, and Configuration > Profiling.
- Number of packets in flow.
- Number of bytes.
- User.
- Domain.
- Fwevent. See
- Fwextcode.
- Profile, e.g. PCs.
- Net device IP address, name and number of flows.
- In-Interface.
- Out-Interface.
See Glossary for more about flow record fields used by GigaFlow.
See also Search for instructions to access the Graphical Flow Mapping feature.
By clicking any Category, Severity, Source IP or Target IP in the Event Entries table, you will be taken to a version of the Events Dashboard filtered for that item.
See Dashboards > Events for an overview of the structure of this page.
Located at Profiling > Traffic Groups.
Traffic groups are subnet and IP range aliases.
- You can assign a name to a subnet or IP range.
- GigaFlow will collect data associated with this range.
- A traffic group can be a subset of another traffic group, e.g. a traffic group spans 172.1.1.0 - 172.1.1.255 and a second traffic group is defined as 172.1.1.80 - 172.1.1.122.
This graph shows the top 10 destination IPs over the past hour.
This graph shows the top 10 destination IPs over the past hour.
This graph shows the top 10 source IPs over the past hour.
This graph shows the top 10 destination IPs over the past hour.
This graph shows the traffic associated with traffic groups over the past hour. The information displayed includes:
- Avg Bits/s: average traffic per second per application.
- Percentage: this is the proportion of all traffic over the past hour seen by a particular traffic group.
- Position relative to the same hour last week: this is the percentage increase or decrease in traffic per second per traffic group compared with the same hour last week.
When more than ten traffic group are registered, the full list can be displayed by clicking the drill down icon. This displays a tabular version of all the data, with a CSV export option.
This graph shows the destination traffic associated with traffic groups over the past hour. The information displayed includes:
- Avg Bits/s: average traffic per second per application.
- Percentage: this is the proportion of all traffic over the past hour seen by a particular traffic group.
- Position relative to the same hour last week: this is the percentage increase or decrease in traffic per second per traffic group compared with the same hour last week.
When more than ten traffic group are registered, the full list can be displayed by clicking the drill down icon. This displays a tabular version of all the data, with a CSV export option.
Reports gives you access to system reports and logs. GigaFlow stores a record of all reports. Reports can be generated in many ways but most commonly by viewing a Forensics page; viewing a Forensics page automatically generates a report. When a report is generated by a user, it is cached by the system and can be accessed again almost immediately. In addition, all recorded reports can be re-run from scratch at any time. Runtimes vary with the scope of the report, i.e. reports that involve more data will take longer to complete. Typical reports for limited periods of time complete in seconds.
Administrators have access to all reports run by all users.
See Configuration > Reporting for more.
Located at Reports > My Current Queries.
My Current Queries lists your queries currently in process. The table includes:
- The user that initiated the report.
- Report source, e.g. Forensics. See Reports > Forensics.
- Report type, e.g. Application. See Forensic Report Types in the appendix.
- Output type, i.e. graph or table.
- When the report was started.
- Runtime.
- Size in bytes.
- Actions: view the cached report or re-run the report from scratch.
The filters used to define the report.
Located at Reports > My Complete Queries.
My Complete Queries lists your completed queries. The table includes:
- The user that initiated the report.
- Source, e.g. Forensics. See Reports > Forensics.
- Report type, e.g. Application. See Forensic Report Types in the appendix.
- Output type, i.e. graph or table.
- When the report was started.
- Runtime.
- Size in bytes.
- Actions: view the cached report or re-run the report from scratch.
- The filters used to define the report.
Located at Reports > All Complete Queries.
This option provides administrators with a view of all queries made by all users.
- The user that initiated the report.
- Source, e.g. Forensics. See Reports > Forensics.
- Report type, e.g. Application. See Forensic Report Types in the appendix.
- Output type, i.e. graph or table.
- When the report was started.
- Runtime.
- Size in bytes.
- Actions: view the cached report or re-run the report from scratch.
- The filters used to define the report.
This option provides administrators with a view of all forensic queries made by all users.
- MyID:
- User: The user that initiated the report.
- Source: Forensics. See Reports > Forensics.
- Report: Report type, e.g. Application. See Forensic Report Types in the appendix.
- Output: Output type, i.e. graph or table.
- Started At: When the report was started.
- Running For: Runtime, so far.
- Request:
Located at Reports > Canceled Queries.
Canceled Queries lists your canceled queries. The table includes:
- Source, e.g. Forensics. See Reports > Forensics.
- Report type, e.g. Application. See Forensic Report Types in the appendix.
- Output type, i.e. graph or table.
- When the report was started.
- Runtime.
- The reason for canceling the report.
- The filters used to define the report.
Located at Reports > Cluster Search.
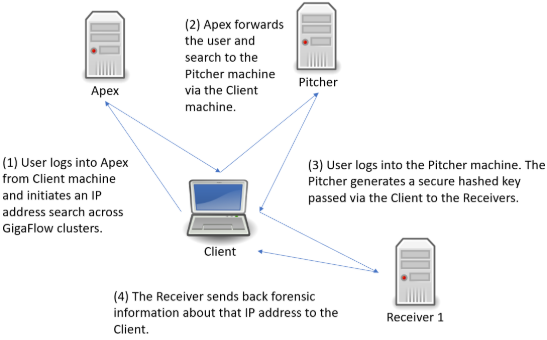
Figure: Conducting a GigaFlow Cluster search
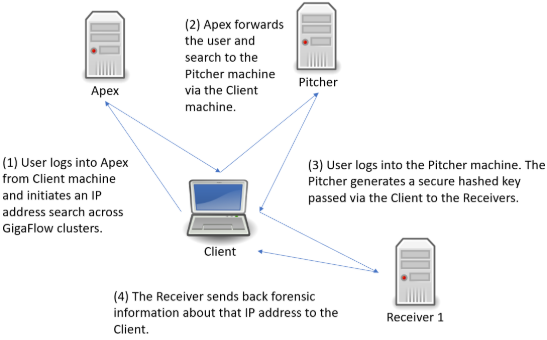
[file: Conducting a GigaFlow Cluster search.]
Following the search link from Apex, you will be brought to a new tab and the log in screen for the Pitcher machine. After logging in, you will be brought to the GigaFlow Cluster report page.
Figure: The initial view of the GigaFlow Cluster report page

This displays a list of hits for this IP address across the cluster; in this example, the IP address 172.21.21.21 was found on 11 devices monitored by three receivers. On these receivers the system found 9 devices with data matching the search and there were no errors.
In the first first table, each GigaFlow server is listed with:
- Server name.
- The URL to connect to the server; follow this link to access the full UI for that particular server.
- The type of result; in this case flows.
- Which device monitored by this server had the data.
- Device details: name, interface and the number of flows seen.
- A number and visualization of the data size; this is a ranking of result relevance.
- A drill-down link to forensics data for each result. A full view into the receiver is displayed below the top table; this allows you to view the results and interact with that GigaFlow server without having to leave this page.
Figure: Clicking on the drill down icon beside a result brings up the full user interface and a forensics report for that device on the associated GigaFlow server

The system allows ten minutes between running the report and viewing these results without re-authentication.
You can also select different report types to run on that device on that GigaFlow server by selecting from the drop-down menu. See Reports > Forensics in the main Reference Manual for more.
Located at Reports > DB Queries.
DB Queries displays a list of the most recent database queries. The information returned includes:
- The database accessed.
- The client requesting the query.
- The start time.
- The query duration.
- Wait events.
- Process ID.
- Query performed.
Located at Reports > Forensics.
See Configuration > Reporting for instructions on how to configure and create new report types. See Appendix > Forensic Report Types for a complete description of the different report types.
Forensics allows you granular, filterable reporting on the stored records. GigaFlow records flow posture, i.e. whether or not a flow is flagged as an excepted event, allowing for detailed analysis.
To create a report:
- Select a report type from the drop-down menu.
- Apply filters to the records to customize output.
- Multiple filters can be selected from the drop-down menu.
- Filters can also be entered using GigaFlow's Direct Filtering Syntax (see below).
- Select the Reporting Period.
- Choose the output type, i.e. graph or table, from the drop-down menu.
- Click on Save if you want to keep your report.
A router - an infrastructure device - has an IP of 192.0.2.1.This router was defined at Configuration > Infrastructure Devices.Choose an Applications report from the report type drop-down menu.Choose Infrastructure Device from the filter drop-down menu.Choose the router from the list of devices and apply the filter by clicking +.
The system will return a graph and/or table with details of:
- Source IP.
- Destination IP.
- Application.
- Bit rate and/or total bits.
- The reporting period is shown at the top right of the main body of the page. This is 2 hours by default.
- On login, the system displays information for the default time period.
- This default time period can be set in Configuration > Reporting in the main menu.
- Different reporting periods can be selected by clicking the from and to boxes.
Queries can be entered directly and quickly using the direct filtering syntax.
Direct Filtering Syntax| Field | Operators | Description | Example |
|---|
| srcadd | =, != | IP Address that the traffic came from. | srcadd=172.21.40.2 |
| dstadd | =, != | IP Address that the traffic went to. | dstadd=172.21.40.3 |
| inif | <, =, >, != | ifIndex of the interface through which the traffic came into the router. | inif=23 |
| outif | <, =, >, != | ifIndex of the interface through which the traffic left the router. | inif=25 |
| pkts | <, =, >, != | Number of packets seen in the flow. | pkts>100 |
| bytes | <, =, >, != | Number of bytes seen in the flow. | bytes<10000 |
| duration | <, =, >, != | Duration of flow in milliseconds. | duration>100 |
| srcport | <, =, >, != | Source IP port of flow. | srcport>1024 |
| dstport | <, =, >, != | Destination IP port of flow. | dstport=5900 |
| flags | <, =, >, != | TCP Flags of flow. flags=2 i.e. syn only. | Flags=CEUAPRSF |
| proto | <, =, >, != | IP Protocol Number/Type. | proto=16 |
| tos | <, =, >, != | TOS Marking. tos=104 | //Flash |
| srcas | <, =, >, != | Source AS Number. | srcas!=5124 |
| dstas | <, =, >, != | Destination AS Number. | dstas!=5124 |
| fwextcode | =, != | Forwarding Extended Code. | fwextcode='out-of-memory' |
| fwevent | =, != | Forwarding Event. | fwevent!='Flow Deleted' |
| tgsource | =, <> | Traffic Group Source. | fwextcode<>'My network 1' |
| tgdest | =, <> | Traffic Group Destination. | tgdest<>'Other' |
- Ranges are also supported for IP address, port and AS fields. i.e. "dstport in (22,23,80,443) will match any flow where the dstport is either of the specified ports.
- Logical operators "and", "or", "not" as well as parentheses can also be used. i.e. "dstport not in(23,2055,443) and srcport not in (8585,23) and (fpr > 0 or pkts < 100)".
- It is possible to check the bit value of a field using the bitand function i.e. "(flags bitand 4)=4" filters for flows with the Reset flag set.
Located at Reports > First Packet Response.
First Packet Response (FPR) is a useful diagnostic tool, allowing you to compare the difference between the first packet time-stamp of a request flow and the first packet time-stamp of the corresponding response flow from a server. By comparing the FPR of a transaction with historical data, you can troubleshoot unusual application performance.
On loading, this page displays any First Packet Response information available for Monitored Servers.
Figure: The First Packet Response reports page

To set up a monitored server, go to Configuration > Server Subnets.
The displayed information includes:
- Device IP address.
- Server subnet.
- Port number.
- Number of clients.
- Number of flows.
- Time and date last seen.
- Basic statistics.
On loading, this page displays any First Packet Response information available for Monitored Servers.
Figure: The First Packet Response reports page

To set up a monitored server, go to Configuration > Server Subnets.
The displayed information includes:
- Device IP address.
- Server subnet.
- Port number.
- Number monitored clients.
- Number of flows, maximum number of clients.
- Maximum number of flows per minute.
- Minimum response time.
- Average response time.

Click the Ticker check box next to a device to enable a ticker in the table below with live response times in milliseconds.
A network audit report is a standard-format JSON object that contains a summary of all the devices registered by GigaFlow that belong to a particular subnet.
Network audit reports are enabled for a particular subnet at Reports > System Wide Reports > Subnet List. Enabling a network audit runs the network audit script for the selected subnet(s). You can view the network audit script at System > Event Scripts.
Server configuration happens at Configuration > Server Subnets.
Located at Reports > Saved Reports.
Newly generated reports of interest can be saved for reference. Click Save  in the top right corner.
in the top right corner.
Once a report has been saved it can be viewed in two ways: (i) open. This opens without running. More filters can be added; (ii) open and run.
Saved Reports are listed with the following information:
- Who created the report.
- Where the report originated, e.g. Forensics.
- Report type.
- Report name.
- Action.
- Description.
- Additional filtering.
- When it was created.
Each automatically discovered server is listed here with:
- Device: this is the IP address of the server.
- Capacity:
- Src Monitored Sessions:
- Src Threshold:
- Dst Monitored Sessions:
- Dst Threshold:
Clicking on a device brings up detailed information for that server.
Details about each discovered server are shown here, with information about its behaviour as a source and destination for traffic. Two tables are shown on screen.
- IP: IP address
- Port:
- Application:
- Flows:
- IP:
- Port:
- Application:
- Flows:
Located at Reports > System Wide Reports.
These are static reports produced by GigaFlow. From the Reports menu, the System Wide Reports option expands to display a further five options:
- SYN Forensics Monitoring
- Device Connections
- MAC Address Vendors
- Subnet List
- Flow Stats
Located at Reports > System Wide Reports > SYN Forensics Monitoring.
GigaFlow monitors all TCP flows where only the SYN bit is set. In normal network operations, this indicates that a flow has not seen a reply packet while active in a router's Netflow cache.
A lonely SYN can be an indicator that:
- Routing was asymmetric. Perhaps the reply returned via a different router.
- Reply traffic was blocked.
- Servers were not responding for some reason.
- Something was probing the network.
GigaFlow creates an alert when:
- SYN Source Network Sweep: alerts if a source IP address fails to get a response from more than IP Address Count Threshold unique destination addresses.
- SYN Source Port Sweep: alerts if a source IP address fails to get a response from more than Port Count Threshold unique destination ports.
- SYN Source Network And Port Sweep: alerts if a source IP address exceeds both Port Count Threshold and IP Address Count Threshold thresholds.
- SYN Destination Unreachable Server: alerts if a destination IP address fails to respond to more than IP Address Count Threshold unique destination addresses.
- SYN Destination Port Sweep: alerts if a destination IP address fails to respond to more than Port Count Threshold unique destination ports.
- SYN Destination Network And Port Sweep: alerts if a destination IP address exceeds both Port Count Threshold and IP Address Count Threshold.
On the SYN Forensics Monitoring page, you can find two tables of information:
- SYN Sources.
- SYN Destinations.
Each table lists the following information:
- Source or destination IP addresses.
- The number of destinations or sources.
- The number of destination ports.
- The number of flows.
- The type of SYN, e.g. network sweep.
- When it was first seen.
- When it was last seen.
See also System > Alerting
Located at Reports > System Wide Reports > Device Connections.
This page lists all known network connected devices. This list is used as a look-up for Layer-2 to Layer-3 connectivity.
The table lists:
- Device.
- Device name.
- Interface.
- Interface name.
- VLAN.
- VLAN ID.
- MAC address.
- IP address.
- User
- MAC vendor.
Clicking the export icon beside the page title creates a .csv file for download or printing.
Located at Reports > System Wide Reports > MAC Address Vendors
This page shows information about devices associated with particular MAC vendors on your network; GigaFlow displays:
- The MAC vendor name.
- The number of times devices from that vendor has been seen, Count.
Click on Count to populate the second table, MAC Addresses. These are the individual devices associated with that vendor. For each device, the table shows:
- Device MAC address.
- When it was last seen on Layer-2.
- When it was last seen on Layer-3.
The Subnet List report summarises all the subnets automatically discovered using SNMP. The details listed are:
- Device Name: the server name.
- Device IP: the server IP address.
- IfIndex: the interface index.
- Name: the interface name.
- Subnet IP: the subnet IP address.
- Subnet: the subnet name.
- Mask: the subnet mask.
- Alias: the subnet alias.
- Description: the subnet description.
- Speed In: the inward bit rate (MB/s).
- Speed Out: the outward bit rate (MB/s).
- Admin: admin status.
- Oper: oper status.
- Audit: audit status.
This report summarises infrastructure devices by flow rate, showing a graph and table listing, for each device:
- Device name and IP address.
- Flow rate (flows per second) and total flows over the report period.
- The maximum flow rate and time it occurred.
- The percentage of the total number of flows over the report period contributed by this device.
Located at Reports > SQL Report.
Select how many of the most recent SQL Queries to view from the drop-down menu, i.e. the most recent 10, 50, 100 or All.
The table lists the following information:
- Query ID.
- Date created.
- User that created the query.
- Name of the query.
- What the query was.
- To run the report with a HTML output, click HTML.
- To run the report with a .csv output, click CSV.
- Click Edit
 to modify the report.
to modify the report. - Click Remove
 to remove the report.
to remove the report.
- To add a SQL report, enter a name and then Save
 .
. - The new report will appear in the SQL Report Filters Table.
- Click Edit
 to open and modify the report.
to open and modify the report.
Located at Reports > User Events.
Select how many of the most recent User Events to view, i.e. the most recent 50, 100, 250 or 500 events.
This table gives information about:
- Event date/time.
- User requesting the event, if you are logged in as an administrator.
- Source IP address.
- Category of event, e.g. a login or a report.
- The action or function performed.
- JSON parameters.
GigaFlow's IpViewer2 uses MapBox to visualise the physical location of IP addresses
- User:
- Device:
- IP:
- Switch:
- Router:
- Bandwidth:
- Apps:
- Bandwidth:
- Hosts:
Figure: The Configuration menu

GigaFlow comes loaded with a standard set of application port and protocol definitions. Flow records are associated with application names if there is a match.
Users can define their own application names within the software and have that application ID (Appid) available within the flow record. There are 3 techniques used, applied in order:
- Customers can define an application profile which lets them match traffic by source/destination IP address, source/destination port, source/destinaton MAC address, protocol, COS and/or nested rules.
- They can assign their own application names to specificed IP ports, i.e. create Named Applications.
- Or, if there are no user defined settings, the software will select the lowest port.
Add Defined Application
- In the New Defined Application section, specify a name, a description and select the flow object that is associated with the application.
- Click Save to add the application.
Add Flow Object
- Specify the flows that make up the object.
Flow Objects are defined by:
- Name.
- Description.
- Device IP address (Device IP).
- Source IP address (Src IP).
- Source MAC address (Src MAC).
- Source Port (Src Port).
- Source Traffic Group.
- Destination IP address (Dst IP).
- Destination MAC address (Dst MAC).
- Destination Port (Dst Port).
- Destination Traffic Group.
- Protocol.
- Class of Service (COS).
- Negate (True/False)
IP addresses, MAC addresses, Ports and Traffic Groups can also be defined as both Source/Destination.
You can add ANDd existing profile(s) to the new Flow Object, i.e. the new definitions are added to the existing profile(s).
You can also select alternative existing profile(s) that this new profile also maps to (ORd), i.e. the new Flow Object uses either the new definitions or the existing Flow Object definitions.
To ANDd or ORd profile(s), use the drop-down menu in the Flow Object definitions and click the +.
As an example, a printer installation at a particular location connected to a particular router can be defined by a Flow Object that consists of:
- A printer Flow Object.
- ANDd a location Flow Object.
- ANDd a router Flow Object.
Or
- The Flow Object could define the IP address of a server and the web port(s).
A second Flow Object can be defined that will have its flow checked against the Allowed profile; this is an Entry profile.
Add Protocol/Port Application
To add a protocol or port application, click the Add protocol/port application icon and enter:
- Name: Name of the application.
- Protocol: the network protocol associated with the application.
- Port: the port number associated with the application.
Click Save.
Already defined applications are listed here. Existing applications can be edited to associate icons.
Already defined flow objects are listed here.
Already defined protocol/port applications are listed here. Existing protocol/port applications can be edited to associate icons.
Located at Configuration > Attributes.
Attributes are aliases used to help with identification of network infrastructure and users. Assigning an attribute category to a MAC address, user, IP, device or interface allows different user groups easily tag and identify your network infrastructure. For example, a network engineer may prefer to alias a device with a name or category appropriate to their view of your network. The security team may prefer a different categorisation.
The categories are:
- MAC Categories
- IP Categories
- User Categories
- Device Categories
- Interface Categories
The aim is to facilitate rapid identification of network infrastructure and user groups.
If you want to add a new device attribute:
- Click Configuration > Attributes
- Click +, Add.
- Enter the new attribute name and category type and then Save
 .
.
Located at Configuration > GEOIP.
You can change the geolocation and IP settings here.
To add new GEOIP overrides:
- Enter comma-separated parameters as follows:
"Start IP,End IP,Country ISO Code,Region Name,Latitude,Longitude"
- or
"IP/MaskBits,Country ISO Code,Region Name,Latitude,Longitude.
A table of existing GEOIP overrides is shown in the table below this.
You can select the number of items to show from the dropdown menu above the table; the default is 50 items.
Information displayed includes:
- Start IP.
- End IP.
- Country ISO code.
- Region name.
- Latitude.
- Longitude.
- List of actions you can perform, i.e. modify or delete entries.
You can also search by entering a country code or clicking on the map below the table.
Located at Configuration > Infrastructure Devices.
Add Device
To add a new infrastructure device:
- Enter the IP address.
- Enter the SNMP community.
- Click Save
 to save changes.
to save changes.
Add Bulk Devices
To bulk-add new devices, i.e. more than one device at a time:
- Enter device information using the format:
ip
- or
ip, communityString
- or
ip, communityString, deviceName
Use a new line for each new device added.
Recheck Forensics
Recheck Forensics by clicking Refresh  .
.
This shows a more detailed version of the Existing Devices table, with additional statistics for each device.
The Existing Device(s) table lists all connected infrastructure devices.
You can select how many of the devices to view, i.e. the most recent 10, 25, 50, 100 or all devices.
At the top of the table, the total number of infrastructure devices is given. You can also search for a particular device. Each column is sortable. The table displays interactive information, including:
- Device ID. To view a detailed overview of this device, click on the IP. See the next section, Detailed Device Information. The Device ID is assigned when the system receives a flow or syslog from it for the first time.
- Device IP address. It is good practice to ensure that the source address is fixed, ideally, to a VLAN or management VLAN address. Otherwise, multiple entries might be created for each alternative pathway.
- SNMP IP: IP address for SNMP access.
- Device name. To change the device name, enter a new name and click Save
 . This defaults to the IP address or the SNMP system name if this exists. Both can be overwritten.
. This defaults to the IP address or the SNMP system name if this exists. Both can be overwritten. - SNMP state, up or down. This indicates whether or not the sender can be polled for more information. To refresh the SNMP state, click Refresh
 .
. - Number of associated Layer-3 interfaces.
- Number of VLANs.
- Number of ARPs.
- Number of BPNs.
- Number of CAM (latest).
- Number of CAMs.
- Number of LLDPs.
- Number of Drops.
- Flows per second. This is GigaFlow's current flow processing rate.
- Number of Flows. This is the total number of flows received by GigaFlow since the last reset or restart, not including duplicates.
- Sampling rate.
- Trigger. This is the flow resolution used in the flows per second calculation.
- Associated Netflow templates.
- Number of forensics.
- Stored MB. This is the storage used for the sender's flow/syslog information.
- GBs. This is the storage limit for the sender's flow/syslog information. When this limit is exceeded, the system will purge the oldest entries.
- Oldest entry.
- Store (yes or no.) See also System > Global > Storage. If the sender's flows/syslogs are stored or not. If not, they will be checked, still, against blacklists and Profilers.
- Associated System Object Identifier (SysOID).
- Number of duplicate flows discarded (if any).
The Device SNMP Mapping table displays:
- System Object Identifier (SysOID).
- Poller. To change the poller, select from the drop-down list and click Save
 .
. - The number of devices using this SysOID.
- A description of the system, e.g. Gigabit Smart Switch.
Located at Configuration > Infrastructure Devices > Detailed Device Information.
By clicking any device IP address in the Existing Devices table, you can bring up a detailed overview of that device.
On loading, the device name, device IP address and device ID are given across the top of the page.
Below this information, you will see the SNMP Settings panel. SNMP information is listed here. This includes:
- Date and time of last SNMP details poll.
- Date and time of last SNMP Interfaces poll.
- Last SNMP duration in milliseconds.
- Date and time of last DSP check.
- SNMP Location.
- Number of interfaces.
- Device description.
- Device ObjectID.
- Device poller.
- Device name.
- Templates, e.g. V5.
- Flows: more detail can be shown by clicking the drill down arrow.
To change the device name:
- Enter the new name in the text box.
- Click Save
 to save changes.
to save changes.
To change SNMP version and/or community:
- Select a version number from the drop-down box.
- Enter a community name.
- Click Save
 to save changes.
to save changes. - Click Test SNMP Fields to test these settings.
To test SNMP settings and status:
- Click Refresh
 to refresh status.
to refresh status. - You will seen a green Up arrow indicating that SNMP is up or a red Down arrow if SNMP is down.
All other device information is populated automatically from the device and cannot be edited.
To add attributes to the device:
- Select a device type from the drop-down menu.
- Enter a name for the attribute and click + to add.
- To remove an attribute, click the small x.
There are quick-links to useful tools, including:
- Forensics.
- ARPs.
- CAMs.
- Int Tools.
- Traffic Overview.
And links to associated integrations (Integrations) and servers (Server Discovery). See also System > Global for more about integrations.
See Reports > Forensics for more.
In this panel, you can view and make changes to the device information storage settings:
- Storage profile name.
- Allowed disk duration, set to 14 days.
- Allowed disk storage (GB). This defaults to 1 GB. To change this, enter a new value and click Save
 .
. - Process flows. You can change this by selecting from the drop-down menu. The choices are:
- Yes.
- No forensics storage.
- No processing.
- Store seen IP, Yes or No.
- Sample rate, per second.
- Time and date of oldest Disk Storage.
- Click Save
 after making a change.
after making a change. - Sample rate. This defaults to 1 millisecond. To change this, enter a new value and click Save
 .
. - To remove a device, click Remove Device.
At the bottom of the detailed infrastructure device settings page, there are several tabs:
- Interfaces.
- Subnets.
- Flow Templates.
- Stats.
- VLANs.
- Bridge Ports.
- Bridge Ports To IF Index.
- Application mapping.
The Interfaces tab consists of an editable table with the following information:
- IfIndex: the interface number.
- The interface name. To change this, enter a new name and click Save
 .
. - The interface alias. To change this, enter a new alias and click Save
 .
. - The interface description. To change this, enter a new value and click Save
 .
. - The interface IP address.
- The interface MAC address.
- Speed In (MB/s). To change this, enter a new value and click Save
 .
. - Speed Out (MB/s). To change this, enter a new value and click Save
 .
. - Admin status.
- Oper status.
The Subnets tab displays a list of SNMP discovered subnets. See also Reports > System Wide Reports > Subnet List.
The Flow Templates tab displays a list of the Netflow templates used, e.g.:
- V9 Templates.
- V10 Templates.
- NSEL Templates.
The Stats tab consists of a list of the number of VLAN, ARP and CAM entries.
The VLANs tab consists of a list of VLANs.
The Bridge Ports tab consists of a list of bridge ports.
The Bridge PortNumbers To ifIndex tab consists of a list of bridge ports.
The Application Mapping tab displays a list of mapped applications with the key, appid and application listed for each mapping.
Enter:
- Name and description. Click Next.
- Client addresses, i.e. devices whose traffic will be monitored. These devices can be identified by IP or MAC Address. You can enter single IP Addresses, range or subnet e.g. 1.1.1.0/255.255.255.0. Or you can enter MAC Address or range e.g. 00:0c:29:82:c8:85,00:0c:29:00:00:00-00:0c:29:ff:ff:ff. Click Next.
- Allowed applications. Select an application from the drop-down list or create a new application at Configuration > Applications.
- Click Submit.
Enter:
- Name and description. Click Next.
- Allowed traffic patterns, i.e. allowed applications/services. Select an application from the drop-down list or create a new application at Configuration > Applications. Click Next.
- Client addresses, i.e. devices whose traffic will be monitored. These devices can be identified by IP or MAC Address. You can enter single IP Addresses, range or subnet e.g. 1.1.1.0/255.255.255.0. Or you can enter MAC Address or range e.g. 00:0c:29:82:c8:85,00:0c:29:00:00:00-00:0c:29:ff:ff:ff. Click Next.
- Allowed server addresses, i.e. servers whose use is allowed. These devices can be identified by IP or MAC Address. You can enter single IP Addresses, range or subnet e.g. 1.1.1.0/255.255.255.0. Or you can enter MAC Address or range e.g. 00:0c:29:82:c8:85,00:0c:29:00:00:00-00:0c:29:ff:ff:ff.
- Click Submit.
Located at Configuration > Profiling.
This is where you can create profiles that define the normal behaviour of your network.
- Profiling is a very powerful feature.
- A Flow Object is a logical set of defined flows and IP source and destination addresses.
- Flow objects make it possible to build up a complex profile or Profiler quickly. These terms are used interchangeably.
- A particular network behaviour that involves network flow objects is described by a Profiler.
To get going, create your first profile.
- A good way to start is to select one type of device and a single IP of this type.
- For example, in retail, this might be a point of sale machine.
- Then build a profile based on expected flows out of the device IP.
- This profile can serve as a template for realtime monitoring; this is an Allowed profile.
Step one is then to create a new Flow Object at Configuration > Applications. To create a flow object:
To create a new Profiler (this term is used interchangeably with profile):
- Go to Configuration > Profiling.
- Give the new Profiler a name and description.
- Select an Entry profile (the profile to be monitored) and an Allowed profile (the acceptable profile) from the drop-down lists. The Entry and Allowed profile selection includes basic flow objects, i.e. individual devices on your network. A profile is a flow object that is itself a combination of flow objects.
- If you want to be alerted when an exception occurs, select Yes from the drop-down menu.
- Click Save.
This table displays a list of existing profiles.
- ID: the profile ID.
- Name: the name of the profile.
- Description: a description of the profile.
- Entry: the Entry profile is the profile that is to be monitored.
- The Entry and Allowed profile selection includes basic flow objects, i.e. individual devices on your network. A profile is a flow object that is itself a combination of flow objects.
- Allowed: the Allowed profile is the target, or acceptable, profile.
- The Entry and Allowed profile selection includes basic flow objects, i.e. individual devices on your network. A profile is a flow object that is itself a combination of flow objects.
- Checks: this is the number of times that the profiles were compared.
- Hits: this is the number of matches between the Entry and Allowed profiles.
- Exceptions: the number of times that the flow records for this profile that have deviated from the ideal, or Allowed, profile.
- Alert: this is set to true or false - if an alert is raised when an exception is detected, this is set to true.
- Actions: profiles can be edited, the exception count can be reset and the profile rank order can be raised or lowered.
Located at Configuration > Reporting.
One of the difficult aspects of reporting on network flows is the number of possible field combinations, with 25+ fields in the extended range. GigaFlow records all fields for all flows with no summarization and no deduplication. GigaFlow allows you to create exactly the report you want.
You can change reporting settings here, in the General and Forensics Reports panels.
Allows you to add new entries to be displayed in the left hand navigation under the Reports option.
You can enter:
- The URL to be called (must be unique).
- The name displayed in the left had menu for this URL.
- Whether this url should be opened in a new window (YES) or the GigaFlow main content frame (NO)
Allows you to import a JSON representation of new entries to be displayed in the left hand navigation under the Reports option.
You can edit the general reporting settings in this panel:
- Default search period: select 1 day, 2 days, 7 days, 14 days or 21 days. The default selection is 1 day.
- Forensics graph summary rows: select 5, 10, 20, 30, 40 or 50 rows. The default selection is 10 rows.
- Default reporting period: the default reporting period is 10 minutes, i.e. the last 10 minutes of information will be presented.
- Maximum number of table rows to return: select 1,000, 5,000, 10,000, 20,000, 50,000, 100,000 or 1,000,000. The default selection is 1,000,000.
- Default Forensics Report: Select which report should automatically run when going from a summary report to a forensics report.
- The default selection is Application Flows.
- Show Cumulative Stacked Chart Values.
- Show Stacked Charts.
- Chart Format.
- Chart Format Custom Settings.
- Click Save Report Settings to save changes or Cancel to clear changes not submitted.
See Appendix > Forensic Report Types for a complete description of the different report types. See also Reports > Forensics for the Direct Filtering Syntax used by GigaFlow.
You can view and clone built-in forensics reports in this panel.
From the Report drop-down menu, select the report type to view or clone. The default selection is Application Flows. In the panel below, you can view:
- The report name.
- The associated table query, in this case:
select srcadd as srcadd,dstadd as dstadd,appid as appid, cast((sum(bytes)*8) as bigint) as bits_total from netflow WHERECLAUSE group by srcadd,dstadd,appid ORDERBY LIMITROW
- The table value field, in this case:
bits_total
- The graph query, in this case:
select FIRSTSEEN as afirstseen,srcadd as srcadd,dstadd as dstadd,appid as appid, cast(sum((bytes)*8)/(MODER/1000) as bigint) as bits_avgsec from netflow WHERECLAUSE group by afirstseen,srcadd,dstadd,appid order by srcadd,dstadd,appid,afirstseen
- The graph time field, in this case:
afirstseen
- The graph value field, in this case:
bits_avgsec
- The graph key field(s), separated by "__", in this case:
srcadd__dstadd__appid
To clone a report:
- Enter the new cloned report name.
- Click Clone Forensics Report to create new cloned report.
- This is a list of existing, editable DSCP names.
- Click Save DSCP Names to commit any changes.
To add a new DSCP name:
- Enter the DSCP number.
- Enter the new name.
- Click Save DSCP Name.
Lists the existing user defined report URLS that are available from the left hand navigation under the Reports option.
The table lists:
- The URL to be called (must be unique).
- The name displayed in the left had menu for this URL.
- Whether this url should be opened in a new window (YES) or the GigaFlow main content page (NO).
Located at Configuration > Server Subnets. See also Reports > First Packet Response.
To begin using First Packet Response (FPR), you must specify the server subnets and ports that you would like to monitor. FPR monitors TCP and UDP traffic, e.g. DNS 53/UDP, and is inherently multi-threaded by device.
To add a new server subnet:
- Click + at the top of the page.
- Enter the subnet address.
- Enter the subnet mask.
- Click Add Server Subnet.
- Click Cancel to clear the data entered.
This tab allows you to view a list of existing monitored server subnets and to add new subnets. The main table displays the following information:
Actions, i.e. edit or delete a subnet. Editing a subnet allows you to specify a particular port to monitor.
This tab allows you to view a list of identified servers on the monitored server subnets. The main table displays a list of the infrastructure devices, routers, involved in transactions to or from the server subnets and associated servers.
This tab allows you to view a list of infrastructure devices, routers, involved in transactions to or from the server subnets and associated servers.
You can select the number of items to show from the drop-down menu above the table; the default is 10 items.
Located at Configuration > Traffic Groups.
Traffic groups are subnet and IP range aliases.
- You can assign a name to a subnet or IP range.
- GigaFlow will collect data associated with this range.
To define a new traffic group:
- Click Configuration > Traffic Groups.
- Existing traffic groups are displayed in the main table.
- Scroll down to create a new traffic group.
To add a new traffic group:
- Enter the name of the new traffic group.
- Enter a description of the new traffic group.
- Enter a start IP address for the traffic group, e.g. 172.1.1.0.
- Enter an end IP address for the traffic group, e.g. 172.1.1.255.
- Is the traffic natted? Yes or no.
Sometimes, it can be useful to define a traffic group by subnet and by infrastructure device. For example, a corporate network could have a subnet served by more than one router. To create a granular view of flow through each router, a separate traffic group could be created for each router, defined by the IP range of the subnet as well as the device name. You can type to filter the device list.
To add a device to a traffic group:
- Click to select a device to associate with the traffic group.
- Click the up arrow
 . to associate this device with the traffic group; the traffic group is now defined by the IP range and the selected device(s).
. to associate this device with the traffic group; the traffic group is now defined by the IP range and the selected device(s). - Click Save.
To bulk-add new traffic groups, i.e. more than one group at a time:
- Enter required traffic group information using the format:
name,description,startip,endip,natted(y/n),deviceIP
Use a new line for each new traffic group.
To edit a traffic group definition, click Configuration > Traffic Groups and click on the traffic group name or on the adjacent drill down icon  . This will bring up a new page for that traffic group where you can edit the group definition.
. This will bring up a new page for that traffic group where you can edit the group definition.
The table of traffic groups shows:
- Name.
- Start.
- End.
- Natted.
- Devices.
- Devices Remaining.
- Hits.
- Src Bytes.
- Dst Bytes.
- Src Pkt.
- Dst Pkt.
To edit a traffic group definition, click Configuration > Traffic Groups and click on the traffic group name or on the adjacent drill down icon  . This will bring up a new page for that traffic group where you can edit the group definition.
. This will bring up a new page for that traffic group where you can edit the group definition.
For each SNMP discovered subnet, the table displays:
- Device.
- Name.
- Device IP.
- IfIndex.
- Name.
- Subnet.
- Action.
- Alias.
- Description.
- Speed In.
- Speed Out.
- Admin.
- Oper.
Figure: The System Settings menu
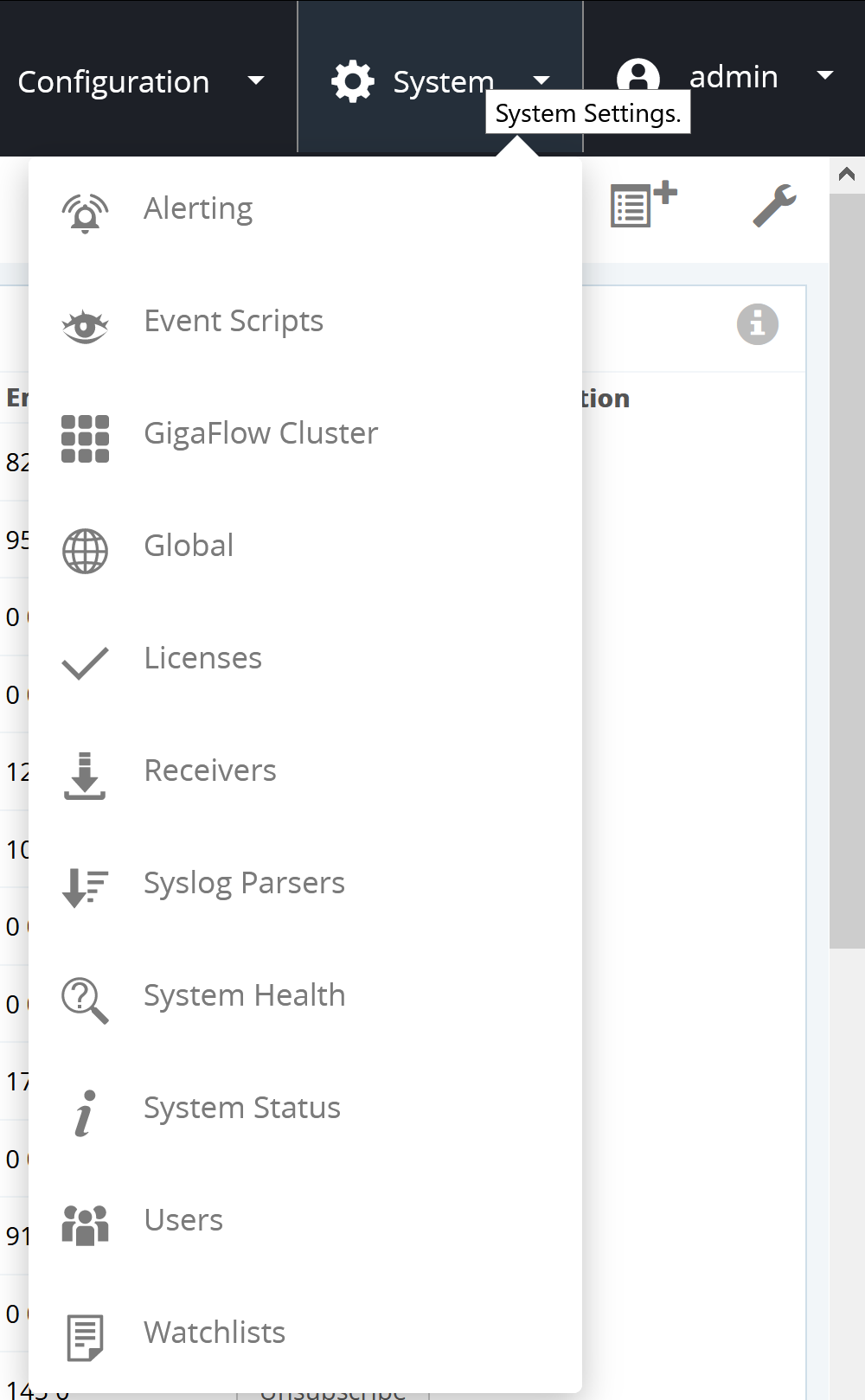
This is where you can make changes to the system settings.
Located at System > Alerting.
Configure GigaFlow to alert you when something happens. Syslog or mail alerts can be set up for any of the following:
- SYN Source Network Sweep: alerts if a source IP address fails to get a response from more than IP Address Count Threshold unique destination addresses.
- SYN Source Port Sweep: alerts if a source IP address fails to get a response from more than Port Count Threshold unique destination ports.
- SYN Source Network And Port Sweep: alerts if a source IP address exceeds both Port Count Threshold and IP Address Count Threshold thresholds.
- SYN Destination Unreachable Server: alerts if a destination IP address fails to respond to more than IP Address Count Threshold unique destination addresses.
- SYN Destination Port Sweep: alerts if a destination IP address fails to respond to more than Port Count Threshold unique destination ports.
- SYN Destination Network And Port Sweep: alerts if a destination IP address exceeds both Port Count Threshold and IP Address Count Threshold thresholds.
- Blacklist source.
- Blacklist destination.
- Profile exceptions.
- A device restarts sending flows.
- A device stops sending flows.
To configure a system log alert:
- Toggle the Yes or No options for any of alert situations.
- You can set and save the server(s) address(es) below. The syslog server(s) input can have multiple entries, separated by a comma, e.g.
172.16.254.1, 172.16.254.2
- Each entry can also have a port, facility and warning level set using the format:
IP_Address:Port:Facility:Level
e.g. 172.21.40.1:515:4:23,172.21.40.2:516:23:4
- In this example, messages are sent to 2 servers; the first is on port 515 and the second is on port 516. Both are using the "Local 7" Facility and the "Warning" level. See syslog at Wikipedia for more.
- Click Save
 to store the server address.
to store the server address. - Sent alerts are displayed with the following information:
- Address.
- Port.
- Facility, e.g. Local 7.
- Level, e.g. Warning.
- Sent.
Sample Syslog Message Types
{"Application":"HTTPS TCP/443","Eventer":"172.0.0.1","Profile":"Facebook","appid":393659,"bytes":1447,"device":"172.0.0.1","domain":"","dstadd":"172.0.0.1","dstport":50561,"duration":288,"eventname":"Profiler","flags":26,"fwevent":0,"fwextcode":0,"inif":12,"macdst":"00:00:00:00:00:00","macsrc":"00:00:00:00:00:00","outif":30,"packets":10,"proto":6,"srcadd":"172.0.0.1","srcport":443,"time":1475147589242,"timeH":"29-Sep-2016 12:13:09.242","tos":40,"user":""}{"Application":"BitTorrent TCP/6881","Black List":"http://lists.blocklist.de/lists/bots.txt","Black List Type":"Source","Eventer":"172.0.0.1","appid":400097,"bytes":120,"device":"172.0.0.1","domain":"","dstadd":"172.0.0.1",
"dstport":63533,"duration":1380, "eventname":"Black List Src","flags":20,"fwevent":0,"fwextcode":0,"inif":12,"macdst":"00:00:00:00:00:00","macsrc":"00:00:00:00:00:00","outif":30,"packets":3,"proto":6,"srcadd"
- "172.0.0.1","srcport":6881,"time":1475147643237,"timeH":"29-Sep-2016 12:14:03.237","tos":40,"user":""}
{"Application":"TCP/49755","Eventer":"172.0.0.1","Syn Type":"Source","appid":442971,"bytes":152,"device":"172.0.0.1","domain":"","dstadd":"172.0.0.1","dstport":54350,"duration":1804,"eventname":"Syn Src Network Sweep", "flags":2,"fwevent":0,"fwextcode":0,"inif":30,"macdst":"00:00:00:00:00:00","macsrc":"00:00:00:00:00:00","outif":12,"packets":3,"proto":6,"srcadd":"172.0.0.1","srcport":49755,"time":1475147666238,"timeH":"29-Sep-2016 12:14:26.238","tos":0,"user":""}{"Application":"TCP/34056","Eventer":"172.0.0.1","Syn Type":"Destination","appid":427272,"bytes":152,"device":"172.0.0.1","domain":"","dstadd":"172.0.0.1","dstport":34056,"duration":1124,"eventname":"Syn Dst Port Sweep","flags":2,"fwevent":0,"fwextcode":0,"inif":14,"macdst":"00:00:00:00:00:00","macsrc":"00:00:00:00:00:00","outif":30,"packets":3,"proto":6,"srcadd":"172.0.0.1","srcport":57058,"time":1475147662254,"timeH":"29-Sep-2016 12:14:22.254","tos":0,"user":""}The IP addresses in these sample Syslog messages have been replaced with 172.0.0.1.
To configure a system email alert:
Toggle the Yes or No options for any of alert situations.Click Save  to store the server address.
to store the server address.
This table lists different possible event triggers with options to: (i) create and event and (ii) trigger a script to run.
The event triggers include:
- Netflow Unknown.
- Netflow TCA.
- Netflow Route Change.
- Netflow Immitigable.
- Netflow Bandwidth.
- Netflow Egress Measurement.
- Netflow Ingress Measurement.
Located at System > Event Scripts.
This is where you can add your own scripts to create new workflows. A table lists existing scripts with the following information:
- Script ID.
- Script name.
- Script description.
- Script length in bytes.
- Who created the script, e.g. Admin.
- Time and date the script was created.
- Is the script currently running? Yes or No.
- The memory occupied by the script.
- How many times the script has been run.
- Average runtime in milliseconds.
- The number of trigger events.
- The number of dropped trigger events.
- The trigger for the script.
- Any errors.
- Actions:
To add a script:
- Click + in the top right.
- Enter a name and description.
- Select a trigger event from the drop-down menu. Possible triggers are:
- Not set.
- 1 Minute.
- 5 Minute.
- 15 Minute.
- All ARP.
- Black List Dst.
- Black List Src.
- Daily.
- Device Restarts Sending Flows.
- Device Stops Sending Flows.
- Hourly.
- Lost Neighbour.
- New ARP.
- New Device.
- New IP.
- New MAC.
- New Neighbour.
- One Off.
- Profile Exception.
- Sys Dst Network and Port Sweep.
- Syn Dst Port Sweep.
- Syn Dst Unreachable Server.
- Syn Src Network and Port Sweep.
- Syn Src Network Sweep.
- Syn Src Port Sweep.
- Syslog.
- Enter the script in the main text box.
- All scripts are JavaScript; the engine is Oracle's Nashorn.
- Click Save
 .
.
Located at System > GigaFlow Cluster.
A single GigaFlow server can be configured to search for IP addresses across many remote GigaFlow servers directly from Viavi's Apex system. This feature is useful for large organisations that may have many GigaFlow servers monitoring different networks within the organisation, e.g. in different regions. The central administrator may want a view across the entire network, e.g. to determine if a particular suspect IP address has been recorded by routers on different networks.
In this example, assume that you are the main administrator and you want visibility on several remote GigaFlow servers.
The set-up is:
- GigaFlow Server #0: this is the server at HQ, used by the main administrator. We call this the Pitcher.
- GigaFlow Server #1: this is remote GigaFlow server #1. We call this Receiver 1.
- GigaFlow Server #2: this is remote GigaFlow server #2. We call this Receiver 2.
- GigaFlow Server #3: this is remote GigaFlow server #3. We call this Receiver 3.
Figure: Defining a GigaFlow cluster
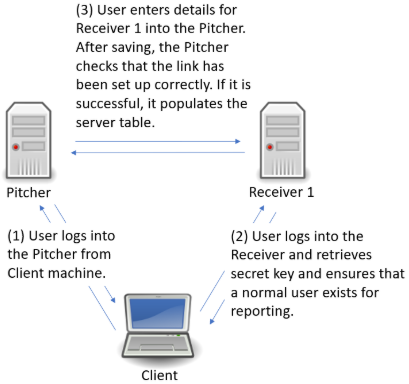
Log in to GigaFlow Server #0, the Pitcher, and navigate to System > GigaFlow Cluster.
In the This Server panel, you will see a pre-generated unique secret. Leave this as is.
In another browser tab or window, log into Receiver 1 (GigaFlow Server #1). Copy the unique secret from Receiver 1's This Server panel. You do not need to do anything with the New Cluster Server panel on the receivers.
Figure: This Server panel
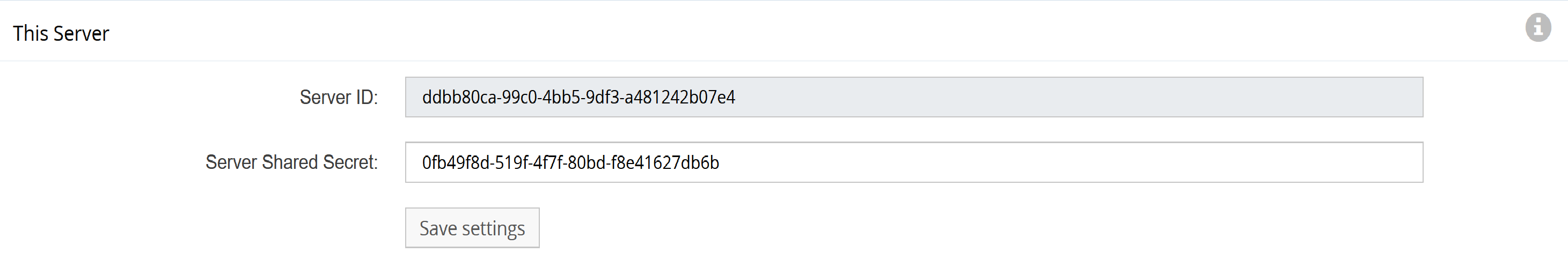
Switch back to the Pitcher (GigaFlow Server #0). In the New Cluster Server panel:
- Enter a name that you will see during a search across servers, i.e. Receiver 1.
- Enter the description that you will see when hovering-over the server name during a search across servers, e.g. "EMEA GigaFlow server (Receiver 1)".
- Enter the full IP address, including port number, used to connect to Receiver 1, i.e. in the format "http(s)://172.1.1.0:22".
- Enter the IP address of the Pitcher system as seen by Receiver 1. This IP address is used by the Pitcher to generate a secure hashed key for communication. The Receiver reverses this hash using, among other things, the IP address of the Pitcher. An intermediate firewall (NAT) could create problems if the Pitcher does not create the hashed key using the IP address seen by the Receiver.
- Enter the UserID used when making superuser calls to Receiver 1, e.g. Admin. This is used during this set-up process.
- Enter the UserID that will be used when making report requests, e.g. reportuser; this is used by all clients when collecting data from the Receiver. This user must exist on Receiver 1. If it does not exist, switch to Receiver 1 and create a new normal user on Receiver 1, i.e. reportuser.
- Paste Receiver 1's secret, i.e. the key copied from Receiver 1's This Server panel.
- Click Save
 to add the Receiver 1.
to add the Receiver 1. - The Pitcher will connect to Receiver 1 using the Admin user to verify that everything is correct and to populate the table at bottom of the System page. Receiver 1 will appear in the main table.
Figure: New Cluster Server panel
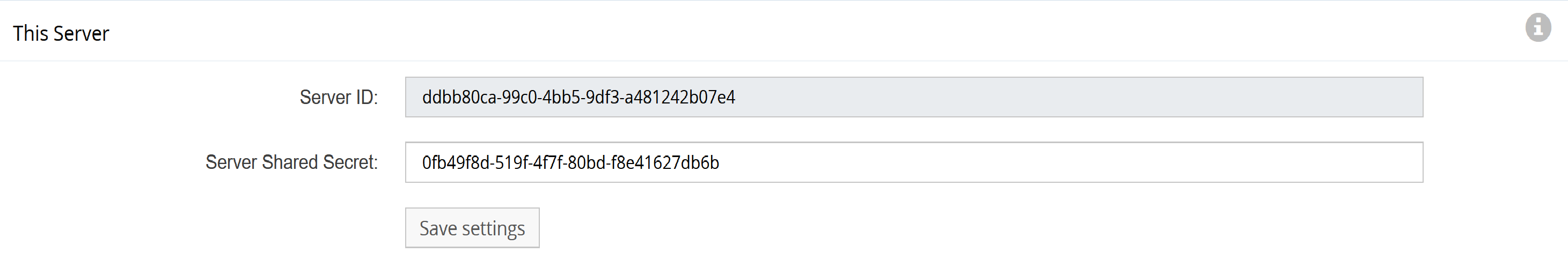
Repeat this process for Receiver 2 and Receiver 3.
The cluster server feature is flexible; a receiver in one cluster can be a pitcher for another.
The Cluster Access panel shows cluster access status. The table lists:
- ID: Cluster ID.
- Added: Time and date.
- By: User.
- Net State: network state, up or down.
- Admin State: admin status, i.e. details on its operation.
- Reporter State: success or fail.
- Settings: JSON object.
- Actions: delete.
Following the search link from Apex, you will be brought to a new tab and the log in screen for the Pitcher machine. After logging in, you will be brought to the GigaFlow Cluster report page. This displays a list of hits for this IP address across the cluster; in this example, the IP address might be found on devices monitored by all three receivers. Clicking on a receiver name brings up the forensics report summary for that IP address from that receiver in the table at the bottom of the summary page. Alongside each receiver on the results page is a link out to that particular server.
Figure: Conducting a GigaFlow Cluster search
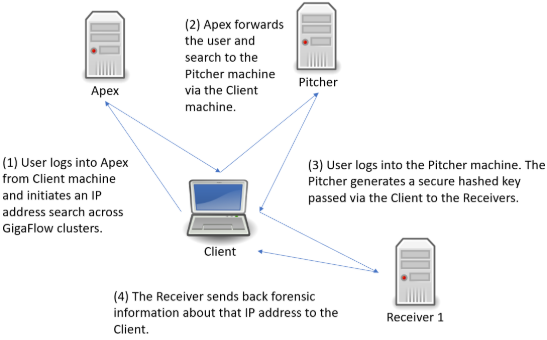
See also Reports > Cluster Search.
Communication between all clients in a Gigaflow cluster is IP to IP, i.e. unicast. The traffic is routed over https, using TLS based on certificates.
New icons along top.
Located at System > Global.
You can find most of the system-wide settings here.
Along the top of the page are quick links to the different settings options. These are:
- General.
- LDAP.
- SSL.
- Import/Export.
- Remote Services.
- SNMP V2.
- SNMP V3.
- Log.
- Proxy.
- MAC Vendors.
- Mail.
- Storage.
- Integrations.
In the General settings box, you can change:
- Server name. This is the name associated with the GigaFlow server and does not have to be the same as the hostname. This is the name used when when the server calls the GigaFlow home servers. It aids identification.
- Theme: light or dark.
- Display IP address on login? Yes or No.
- Max number of First Packet Response Clients. This is the maximum number of First Packet Response clients supported by the system and any one point in time. 400 is the default.
- Max memory IPs, 300,000 by default. This is the maximum number of IP addresses that can be cached in RAM before writing to disk. It functions as a memory table lookup for GigaFlow Search. In general, there is no need for you to change this. The aim is to reduce disk read and writes.
- TCP Testing Ports, e.g. 22, 23, 80, 443, 3389, 1143, 21.
- TCP Testing Timeout, e.g. 200 ms.
- TCP Port Threads, e.g. 4.
- TCP Device Threads, e.g. 4.
- TCP Syn Port Threshold, e.g 5.
- TCP Syn Address Threshold, e.g 10.
- Duplicate Cache Size, e.g 90. This is the number of flows that each devices should cache in order to try and detect duplicates. It will use the start/end time, src/dst port and IP address as well as the byte and packet count to match.
- Process Duplicate Flows: Yes or No.
- Ignore Duplicates On Summaries: Yes or No.
- SNMP Timout: 2000 milliseconds.
- Server Discovery Limit: default is 100 servers.
- Server changes require a system restart.
- Server Auto Discovery Enabled: Yes or No.
- Web Session Timeout: default is 30 minutes.
Before you can authenticate users using LDAP or AD, you must set the LDAP (Lightweight Directory Access Protocol) server.
Examples for an LDAP server integration :
- Server address, e.g. ldap://172.21.40.189:389.
- LDAP Group DN, the branch that should be searched to return a list of groups from e.g. ou=observer,dc=viavi,dc=solutions
- LDAP Group Field, the dn of the field to return e.g. entryDN
- LDAP Group Search,the filter to use when searching for groups e.g. (&(objectClass=groupOfNames))
- LDAP Group Search Filtered, the filter to use in the users page when filterling the list of available groups e.g. (&(objectClass=groupOfNames)(cn=$FILTER))
- LDAP User DN Base, the branch from which to search users e.g. ou=users,dc=viavi,dc=solutions
- LDAP User DN Field, the DN for the users e.g. entryDN
- LDAP Users Group Field, the filed representing the users group membership e.g. memberOf
- LDAP User Filter,the filter to apply when searching for users e.g. (&(objectClass=inetOrgPerson)(uid=$USERID))
- Username, the dn of the user to bind when searching the server e.g. cn=admin,dc=viavi,dc=solutions
- Domain Name, not required for NON AD servers e.g. LEAVE BLANK
- Password, e.g. XXXXXXXXXX
- Status, i.e. if the connection is good and how many LDAP groups have been retrieved.
Examples for Active Directory server integration :
- Server address, e.g. ldap://172.21.40.189:389.
- LDAP Group DN, e.g. dc=anuview,dc=net
- LDAP Group Field, e.g. distinguishedName
- LDAP Group Search, e.g. (&(objectClass=group))
- LDAP Group Search Filtered, e.g. (&(objectClass=group)(cn=$FILTER))
- LDAP User DN Base, e.g. dc=anuview,dc=net
- LDAP User DN Field, e.g. cn
- LDAP Users Group Field, e.g. memberOf
- LDAP User Filter, e.g. (&(objectClass=user)(sAMAccountName=$USERID))
- Username, e.g. Administrator
- Domain Name, e.g. anuview.net
- Password, e.g. XXXXXXXXXX
- Status, i.e. if the connection is good and how many LDAP groups have been retrieved.
In the SSL settings box, you can view and select or change:
- Existing certificate aliases.
- Keystore location on the network or server. Leave this blank for default setting.
- Keystore password. Leave this blank for default setting.
- Click Save Keystore Settings.
Saving will restart the HTTPS service which may take up to one minute.
The Import and Export windows allow you to easily import or export all of your GigaFlow configuration and system settings.
To import GigaFlow configuration and system settings:
- Click Import
- Copy the text version of the new configuration and system settings.
- Paste this text into input window.
- Click Save new configuration and system settings to enter and save the new configuration and system settings.
To export your GigaFlow configuration and system settings:
- Use the first icon from the left, above the main tabs, to Export configuration and system settings.
- Copy and paste this text into a text editor, e.g. Notepad, and save it.
ZeroMQ
- Status: default, Not Configured.
- Listener: default, '*.5555.
- Cache Period (milliseconds): default, 60000.
- Cache Size: default, 100000.
- Max Flows Transmitted Per Message: default, 100000.
- Max Seconds Per Message: default, 60000.
- Message Store:
- Restart required.
- Message Store Max Size MB: default, 50000.
Save ZeroMQ Settings.
Observer GigaStor
- URL.
- Display.
- User Name.
- Password.
- Status.
- Actions.
Kafka
- Status: No status for now.
- Broker: enter the Kafka broker address.
- SSL Trust Store: path to trust store.
- Trust Store Pass: password.
- Topic: default, gigaflowraw.
- Group ID: group name.
- Cache Period (milliseconds): default, 300000.
- Cache Size: 5000.
Save Kafka Settings.
Syslog Forensics
- Status: for example, has sent w packets , x dropped, y largest, z, longest t (ms).
- Format: Text or JSON.
- Storage Buffer: 10000.
- Server: IP address and port in the format xxx.xxx.xxx.xxx:xx
- A change requires a restart to affect all devices.
- Cache Period (milliseconds): 300000.
- A change requires a restart to affect all devices.
- A change requires a restart to affect all devices.
Save Syslog Settings.
Click the second icon from the left, above the main tabs, to add an SNMP v2 Settings Commuity.
- Enter the community name in the text box and click Save.
SNMP allows GigaFlow to poll sending devices. GigaFlow supports multiple concurrent pollers. Each device is serviced every 30 minutes. SNMP polling is used to retrieve:
- Device information, i.e. location, sysOID, interface names, descriptions, aliases and IP addresses.
- ARP table for IP address to MAC address to interface mapping.
- CAM table for MAC to switch port mapping.
In the SNMP V2 settings box, you can add or delete new SNMP V2 community strings. To add or delete a community string:
- Delete existing communities by clicking the delete icon.
Click the third icon from the left, above the main tabs, to add an SNMP v3 Settings Commuity.
- Enter the new SNMP V3 community name.
- Enter a user name.
- Authentication Type, i.e. MD5 or SHA secure hash functions.
- Enter an authentication type password.
- Privacy Type, i.e. AES-128, AES -198, AES-256, DES or 3DES.
- Enter a privacy password.
- Enter a context. SNMP contexts provide VPN users with a secure way of accessing MIB data. See Cisco and the Glossary for more.
- Submit by clicking Save.
SNMP allows GigaFlow to poll sending devices. In the SNMP V3 settings box, you can view and delete SNMP v3 community strings.
In the Log settings box, you can view the log file and change the logging level:
- Click on Log File to view the log file entries.
- Select a logging level from the drop-down menu, i.e. DEBUG, INFO, ERROR, FATAL, WARN.
- Click Save
 to save changes to the logging level.
to save changes to the logging level.
These are the proxy settings used to access GigaFlow's homeworld server. The information is required for several reasons: (i) to allow GigaFlow to call home and register itself; (ii) to let us know that your installation is healthy and working; (iii) to update blacklists. All calls home are in cleartext. See System > Licences for more.
- Server ID. This is the unique server ID; it is sent in calls home.
- Proxy address. Leave blank to disable proxy use.
- Proxy port, e.g. 80.
- Proxy user.
- Proxy password.
- Click Test Proxy Settings to test the proxy server.
- Click Save Proxy Settings to save the settings.
Click the fourth icon from the left, above the main tabs, to add a MAC Vendor. To add a new vendor prefix:
- Enter a MAC address.
- Enter the prefix length in octets, i.e. 12 for the full address, 10 leftmost octets, 8 leftmost octets, 6 leftmost octets or 4 leftmost octets.
- Enter the vendor name, e.g. Dell.
- Click Save to save changes.
Existing vendor prefixes are displayed in the table below alongside the date created and available actions, i.e. modify or delete.
If you are using email alerts, you can configure email here. To set up email:
- Change Enabled from No to Yes.
- Enter the email address that GigaFlow will send email from.
- Enter the email address of the user receiving GigaFlow alerts.
- TLS (transport layer security)? Yes or No. See Glossary for more about TLS.
- Enter the mail server username.
- Enter the mail server password.
- Enter the mail server address.
- Enter the mail server port number, e.g. 25.
- Click Test Mail Settings to test the email server.
- Click 'Save Mail Settings to save changes.
Storage Settings
In the Storage settings box, you can make changes to the following settings:
- Monitor Drive Space: enable or disable drive space monitoring, i.e. Yes or No.
- Drive To Monitor: set the drive to monitor, e.g. C:/.
- Min Free Space (GB): set the minimum free space allowed (GB).
- Default Device Storage Space (GB): set the default device storage space (GB).
- Min Forensics Storage (Days): set the minimum forensics storage (Days), e.g. 21. After this time, flowsec records will be deleted.
- Requires 720 MB or 15 per hour.
- See Disk Usage by Device', below.
- Max Forensics Storage (Days):
- Cannot determine how many tables may be generated as value =0.
- IP Search Storage (Days): set the IP search storage (Days), e.g. 21. After this time, IP address history will be deleted.
- Forensics Storage Threads:
- Forensics Table Cache Size: set the forensics table cache size, e.g. 10,000. This is the number of entries cached before writing to disk.
- Forensics Table Cache Age (ms): set the forensic table cache age (milliseconds), e.g. 10,000. After 10 seconds, the forensic data is written to disk.
- Forensics Cache Storage: set the forensic cache storage size, e.g. 40,000.
- Forensics Indexes: enter forensics indexes. This is a comma-delimited list of forensics table field names, e.g. "srcadd,dstadd,appid". See Reports > Forensics in the Reference Manual for more.
- Enter forensics indexes
- Forensics Rollup Age (Days): set the forensic rollup age (Days), e.g. 4 days, period after which data should be rolled into daily tables.
- Forensics Rollup Location: set the forensics rollup location.
- Event Storage Period (Days): set the event storage period (Days), e.g. 100 days, how long events should be recorded for.
- ARP Storage Period (Days): set the ARP storage period (Days), e.g. 100 days, how long ARP entries should be recorded for.
- CAM Storage Period (Days): set the CAM storage period (Days), e.g. 100 days, how long ARP entries should be recorded for.
- Event Summary Storage Period (Days): set the event summary storage period (Days), e.g. 200 days.
- Interface Summary Storage Period (Days): set the interface summary storage period (Days), e.g. 200 days.
- DB Fetch Size:
- Allow Unlogged flow tables:
- Auto-tune PostgreSQL: enable or disable Auto Tune of the Postgres database. Yes or No.
- Archive Folder Location:
- Enter Archive Folder Location
- Archiving Enabled :
- TCP Syslog Threads:*
- TCP Syslog Buffer Size*
To commit changes, click Save Storage Settings.
Disk Usage by Device
The following information is given for each flow device:
Netflow
- Device: device name.
- Largest Time: date and hour.
- File Window: hours.
- Total MB.
- % of All.
- Average File MB.
- Average Per Day MB.
- Largest Size.
The minimum Forensics Storage is 21 days. Forensics data is stored in tables for up to four hours to speed up search and reporting. These tables are rolled into one-day tables after the Forensics Rollup Age period; this is four days by default. (see System > Global.) This is a minimum period.
It is important to set aside space for drive monitoring. GigaFlow will fill the disk drives until the pre-defined minimum amount of free space is left. GigaFlow caps the storage that any particular device is using for forensics data; this is 50 GB by default. This cap can be changed globally and on a per device basis which in turn sets an overall cap on the amount of space used by GigaFlow.
Data Retention and Rollup| Type | Resolution | Table Duration (default) | Retention | Setting Involved |
|---|
| Raw Flows | millisecond | 1 hour-1 day | 21 days | Min Free Space, Default Device Storage Space, Min Forensics Storage, Forensics Rollup Age. |
| IP Search | millisecond | 1 day | 21 days | IP Search Duration. |
| Events | millisecond | 4 hour | 100 days | Event Storage Period, Event Summary Storage Period. |
| ARP | millisecond | 1 day | 100 days | ARP Storage Period. |
| CAM | millisecond | 1 day | 100 days | CAM Storage Period. |
| Interface Summaries | Minute | 2 day | 200 days | Interface Summary Storage Period. |
| Traffic Summaries | Hour | 7 day | 200 days | Interface Summary Storage Period. |
An integration allows you to call defined external web pages or scripts directly from the Device Interface Overview page. To add an integration, navigate to System > Global. In the Integrations settings box, you can add or change an integration.
There are two types of integration:
- Device: where you can pass the device IP address.
- Interface: where you can pass the device IP address and the ifIndex of the interface being used.
To add an integration:
- Click on the Add Integration icon, fifth from left at the top of the page.
- Enter a new name, e.g. "Interface Action 1".
- Select the type of target, i.e. a device or an interface. These map to the IP address of the device and the ifIndex of the interface.
- Select the type of action, i.e. will the integration work with a web page or a script.
- Enter the web page URL or select a script.
- Enter inputs to be passed via the website or script.
- Click Save
 to save changes.
to save changes.
Example 1
In the code below, the populated field tells the software that you want to populate the device field with the IP address and the ifindex field with the ifindex. These fields (device and ifindex) will be passed to the target. We also have required fields, which are fields which the user is required to populate.
{'populated':{'device':'flow_device','ifindex':'flow_ifindex'}, 'required':[{'name':'user','display':,'type':'text','value':},{'name':'password','display':'Password','type':'password'},{'name':'macro','display':'What Macro?','type':'select','data':['macro1','macro2','macro3','macro4']}]}
Example 2:
var ProcessBuilder = Java.type('java.lang.ProcessBuilder');var BufferedReader = Java.type('java.io.BufferedReader');var InputStreamReader= Java.type('java.io.InputStreamReader');output.append(data);output.append("Device IP:"+data.get("device")+"");output.append("IFIndex:"+data.get("ifindex")+""); try { // Use a ProcessBuilder //var pb = new ProcessBuilder("ls","-lrt","/"); //linux var pb = new ProcessBuilder("cmd.exe", "/C", "dir"); //windows output.append("Command Run"); var p = pb.start(); var is = p.getInputStream(); var br = new BufferedReader(new InputStreamReader(is)); var line = null; while ((line = br.readLine()) != null) { output.append(line+""); } var r = p.waitFor(); // Let the process finish. if (r == 0) { // No error // run cmd2. } output.append("All Done"); } catch ( e) { output.append(e.printStackTrace()); } log.warn("end")Click the Add Observer GigaStor icon; this is the last icon at the top of the page. Then enter:
- Display Name:
- URL:
- User:
- Password:
And click Save.
Located at System > Licenses.
Here you can view all the licences associated with GigaFlow.
The GigaFlow License table lists:
- This Server ID.
- First run, date and time.
- Customer name.
- Product name.
- Expiration date of license.
- Duration of license.
- Number of flow devices.
- Number of flows per second.
- You can enter a new license in the text box at the end of this table. Click ADD to submit.
The license is also viewable as a JSON object at the bottom of the page.
All 3rd party licenses are listed in the next table. These are:
All communications between your installation of GigaFlow and our servers are carried out in cleartext over HTTP; you have complete visibilty. You can view call home data at System > Licenses.
All communications between your installation of GigaFlow and our servers are carried out in cleartext; you have complete visibilty. You can view call home data at System > Licenses.
A typical response to a call home might look like. You can view call home response data at System > Licenses.
You can view all call home errors at System > Licenses.
JSON object version of GigaFlow license.
Add Port and Netflow Processing Threads links at top of page.
Located at System > Receivers.
Here you can view and edit GigaFlow's defined Netflow receivers.
It is important to ensure that the installation is ready to listen. Senders on your network will be configured to send to the GigaFlow server address and to a defined port; these must match the receivers.
GigaFlow is built to receive and process flow records and session-based syslogs. GigaFlow can also process syslog messages relating to specific user or IP authentication details.
Flow records are processed automatically into the flow databases. The records are also checked against blacklisted IPs and against defined Profilers. See System > Blacklists and Profiling.
The syslog messages are sent to the syslog processor for parsing.
Here you can see the existing listener ports available and if they are receiving flows or syslogs.
You can select the number of ports to show from the dropdown menu above the table, i.e. 10, 25, 50, 100 or all. The default is 50 items. The total number of ports is displayed at the top of the table. The information displayed includes:
- Port number.
- Port type.
- Any associated settings.
- Minimum, maximum and average number of packets.
- Status, i.e. running, yes or no.
- Action: delete
 or stop
or stop  Stop icon..
Stop icon..
To add a new port, click the + icon at the top of the page. Then:
- Enter the new port number.
- Enter the new port type.
- Enter the new port source mask. This mask is applied to the IP address of the source device. It can be useful to consolidate multiple flow senders into virtual source device(s). Leave blank for no summarization.
- Click Save to create and save.
To edit the number of Netflow processing threads, enter the new number and click Save.
The Port Threads table displays summary information about the port threads. This includes:
- Port number.
- Type, e.g. V5, V9.
- Thread.
- Devices.
- Received packets.
- Dropped packets.
- Current packets.
- Ignored packets.
- Max packets.
Infrastructure visibility is achieved using session-based Syslog. Located at System > Syslog Parsers.
System log parsing rules can be viewed and edited here.
All existing syslog parser patterns are listed here. Information displayed includes:
- ID.
- Name.
- Description.
- Type.
- Fields.
- Actions, e.g. edit or delete.
Default system Syslog parser patterns are listed here. Information displayed includes:
- ID.
- Name.
- Description.
- Hits.
- Misses.
- Took.
- Actions, e.g. edit or delete.
Click + to add the corresponding Syslog parser from the drop-down menu.
System Syslog exceptions are listed here. Information displayed includes:
- Time.
- Source IP.
- Data about the exception.
Located at System > System Health.Here you can find timelines of:
- DNS cache size.
- All users size.
- Users-to-IP size.
- Forward event codes size.
- forward extended codes size.
- Deduplication size.
- Free swap space size.
- Total physical memory size.
- Total used Java memory size.
- Committed virtual memory size.
- Free physical memory size.
- Total swap space size.
- Total vs. free memory size.
- Total used Java memory size.
- CPU load.
- Flows per second.
- Receiver drops.
- Receiver ignored.
- Free disk space.
- Connected device stops sending flows (remove?).
Located at System > System Status.
- Limit: 25 is the default number of items to show. Other options are None, 10, 25, 50, 100, 200, 500 and 1,000.
- Refresh: 5 seconds is the default refresh time. Other options are Never, 1 second, 5 seconds, 10 seconds, 30 seconds and 1 minute.
- You can enter a regular expression to filter log entries.
- Click Submit to update the log file viewer settings.
This page displays memory performance. The start time and uptime are displayed prominently at the top of the page.
The main table lists:
- IPs, active and total.
- IP window, e.g. 0 seconds.
- Used memory (bytes).
- Total memory (MB).
- Number of devices.
- Number of MACs.
- Maximum memory (MB).
- Percent memory used.
- Free memory (MB).
- Number of MACs For Prefix 6. Click List to list them.
- Number of MACs For Prefix 7. Click List to list them.
- Number of MACs For Prefix 9. Click List to list them.
- Number of MACs For Prefix 12. Click List to list them.
- You can go to relevant sections of the Log Viewer and to First Packet Response by clicking the links below. See System > System Status and Configuration > Server Subnets for more.
The Stats sections details:
- Number of devices.
- Latest flows per second.
- Average flows per second.
- Kafka Enabled: Yes or No.
- Syslog Forensics Enabled: Yes or No.
- Server Discovery: default, Server Discovery by Device. Click to open a new table.
- Syslog Forensics Flows: default, Syslog Forensics Flows. Click to open a new table.
- PENs: click to refresh.
- DNS cache: click to delete.
- Users seen.
- Users seen to IP address.
- Event codes.
- Ext codes.
- App IDs.
- De-duplication codes.
- Syn sources reports.
- Syn destinations reports.
- Loaded Netflow archives.
- Netflow tables.
- Oldest Netflow data.
- Oldest Netflow device.
- Oldest Netflow realtime.
- FlowSec tables.
- Oldest flowsec data.
- Oldest event summary.
- MB per day for forensics.
- MB per day for flowsec.
- Largest tables all forensics by device: click to open new table.
This page displays the performance of database connections. The database start time and uptime are displayed prominently at the top of the page.
The DB connections table lists the most recent database connections. See PostgreSQL documentation for more.
Select how many entries to view from the drop-down menu, i.e. the 10, 50, 100 or All. The default selection is 50.
The table lists:
- Database name.
- Client.
- Start time.
- Duration of connection.
- Waiting.
- Process ID.
- Query.
- Action, i.e. Remove.
You can view any PostgreSQL database deadlocks to help with troubleshooting performance problems. See PostgreSQL documentation for more. The table lists:
- The name of database involved.
- The relation involved. This is an internal PostgreSQL object identifier.
- The ID of the transaction targeted by the lock, or null if the target is not a transaction ID.
- The name of the lock mode held or desired by this process.
- If the lock was granted or not: this is true if the lock is held, false if the lock is awaited.
- The user that initiated the transaction.
- The query involved in the transaction.
- The start time of the transaction.
- The age of the transaction.
- The process ID of the server process holding or awaiting this lock, or null if the lock is held by a prepared transaction.
This page displays named table performance. The start time and uptime are displayed prominently at the top of the page. See PostgreSQL documentation for more.
Select how many entries to view from the drop-down menu, i.e. the 10, 50, 100 or All. The default selection is 10. You can also search for specific tables.
This page displays prepared table performance. The start time and uptime are displayed prominently at the top of the page. See PostgreSQL documentation for more.
Select how many entries to view from the drop-down menu, i.e. the 10, 50, 100 or All. The default selection is 10. You can also search for specific tables.
Located at System > Users.
New Add links along top of page.
Here you can view and edit information for all GigaFlow users and user groups. There are three categories of user on GigaFlow:
- Local users; these are users set up for the particular GigaFlow installation.
- LDAP users; these are network users authenticated by LDAP.
- Portal users; these are users identified by a username and IP address. Portal user access is useful for programmatic access to the system, i.e. scripts.
Select how many entries to view from the drop-down menu, i.e. the 10, 50, 100 or All. The default selection is 10. You can also search for specific usernames or IDs using the search box.
All users are listed here. Information displayed includes:
- Name.
- Login ID.
- User type. Local users exist in the local database only. LDAP users were entered locally but authenticated against the LDAP server.
- User specific settings.
- User password.
- Actions, i.e Remove user, Edit user or Change Password.
To add a new local user:
- Enter the email address of the new user. This is the same as the login name.
- Enter a display name for the new user.
- Select a user role from the drop-down menu, e.g. normal or administrator.
- Enter a password for the new user.
- Click Add User to add the new user.
To add a new user group:
- Enter the new user group name.
- Select abilities to associate with the new user group.
- Click Add User Group to add the new user group.
This table lists all existing user groups along with associated abilities.
For each user group:
- Click the small x beside an ability to remove it.
- Select new abilities from the drop-down menu to the right and click Add to add abilities to a user group.
Information displayed includes:
- Name.
- Settings.
- Actions, e.g. Edit user or Remove user.
Enter the domain name and ID of the user you want to allow to log into the system. They will be added as normal users.
To add a new LDAP user:
- Enter the new user ID.
- Enter the new user domain.
- Click Add LDAP User.
To add a new LDAP user group:
- Select a group from the drop-down menu.
- You can also apply a filter to limit number of available groups. Enter filter text and click Apply LDAP Filter. (You can use *filter text* for wild card searches.)
- Select user role, e.g. normal or administrator.
- Click Add LDAP Group to add the new LDAP group.
Information displayed includes:
- Name.
- Settings.
- Actions, e.g. Edit user or Remove user.
- Select how many entries to view from the drop-down menu, i.e. the 10, 50, 100 or All. The default selection is 10. You can also search for specific usernames or IDs using the search box.
Information displayed includes:
- Login ID.
- IP address.
- User name.
- Actions, e.g. Edit user or Remove user.
To add a new portal user:
- Enter the new IP regular expression.
- Enter the new user regular expression.
- Click Add Portal User.
This table lists all of the currently configured Data Access Groups.
For each Data Access Group:
- You can see the number of traffic groups allowed under the entries column.
- Remove the traffic group
- Click Edit to Edit the group.
This function allows you to apply a filter to the data a user requests automatically. These filters are based on Traffic Groups and a user can have access to many Traffic Groups using this feature.
To add a new Data Access Group:
- Enter a unique name for this group.
- Enter a description for this Data Access Group
- Click Add Access Group to add the new Access group.
Once added, you can edit the group to control which Traffic Groups are assigned to it, in the Users own settings you can then assign them to any available Data Access Group.
Located at System > Watchlists.
GigaFlow uses a blacklist compiled from multiple online sources. These lists are retrieved every hour and merged into a list of about 30,000 potentially dangerous IP addresses. Your GigaFlow system checks this hourly-updated list every five minutes and updates the local list when necessary.
We are reviewing our code watchlist terminology and will update this documentation to reflect any changes.
This table lists the online blacklists available with relevant information. Information includes:
- The source URL of the blacklist.
- The size, in number of entries, of this blacklist.
- Confidence level assigned to this blacklist, i.e. your confidence in its completeness and accuracy.
- Severity or importance assigned to this blacklist.
- The date and time of the last update.
- The provider of the blacklist, defaulting to Gigaflow.
- The number of entries.
- The total number of events related to each blacklist.
- You can unsubsribe from any blacklist.
To add a new blacklist source:
- Click the Add Whitelist Source icon, first from left at the top of the page.
- Enter the URL of the new blacklist.
- Enter a display name for the new blacklist.
- Enter the importance (or severity) of the new blacklist.
- Enter your confidence in the new blacklist, i.e. your confidence in its completeness and accuracy.
- Enter a refresh rate in minutes (defaults to 1 minute).
- Click Subscribe to add the new blacklist source.
- Click the Blacklist Actions icon, last from left at the top of the page.
To refresh blacklists automatically, select Yes.
GigaFlow can alert on flow entries that match known bad IP addresses, scanning or outside profiles. Whitelisting provides the facility to tell the checking mechanism in GigaFlow that particular IPs or subnets should not raise an exception on any of the defined conditions. When defining a whitelist you should specify a reason for excluding a host or hosts. If you set the IP address to that of the infrastructure device and the mask to zero, GigaFlow will whitelist all traffic for the device.
The whitelist table shows a list of the current whitelisted items, including the following information:
- Address.
- Mask.
- Entered.
- User.
- Reason.
- Hits, i.e. the number of matched flows to that item.
- Action.
You can select the number of items to show from the dropdown menu above the table; the default is 50 items.
To add a new whitelist entry:
- Click the Add Whitelist Entry icon, second from left at the top of the page.
- Enter IP address of whitelisted site.
- Enter its IP mask.
- Enter a reason for its whitelisting.
- Click Add.
The locally defined blacklist table shows a list of the existing locally-defined blacklists, including the following information:
- The source blacklist.
- The blacklist category.
- The size of the blacklist; this is the number of entries on the list.
- Your confidence in the black list, i.e. your confidence in its completeness and accuracy.
- The importance (or severity) of the blacklist.
- The provider of the blacklist.
- Entries.
- Action.
To add a new local blacklist:
- Click the Add Local Blacklist icon, third from left at the top of the page.
- Enter a category, or name, for the blacklist.
- Enter the importance (or severity) of the new local blacklist.
- Enter your confidence in the new local blacklist, i.e. your confidence in its completeness and accuracy.
- Click Subscribe to add the new local blacklist.
- After submitting the local blacklist, enter IP addresses, separated by a comma or on a new line in the Entries text area and click Save.
Adding a noproxy=true flag to a watchlist URL allows the system to bypass proxy servers and access the list directly, i.e.
{URL to file}?NOPROXY=true






 .
.












 . This provides a complete overview of that flow, listing:
. This provides a complete overview of that flow, listing: